How to secure your linux pc by encrypting your hard drive

Daniel Hoffman
Published Mar 29, 2026
There’s bound to be data on your computer that you want to protect from hackers, nosy friends, or curious colleagues. Encrypting your computer drive protects you from intruders, and here’s a couple of different ways to secure your data.
For today’s lesson we’ll show you how to secure data by encryption a partition, a folder, and also how to create a hidden volume with TrueCrypt.
Encrypting a Partition
Ubuntu’s alternate CD installation wizard gives us an option to encrypt our Ubuntu installation partition, so you’ll want to burn the ISO file into a live disk or create a bootable USB drive and install Ubuntu with it.
Ubuntu’s alternate installation menu is very similar to your standard Ubuntu installation menu. The installation wizard will ask you to choose your language, keyboard, network, and the most important step is the partitioning method where we need to choose the ‘Guided – use entire disk and set up encrypted LVM’ option to encrypt our entire hard disk.
Please note that we have to provide a ‘Master’ and not ‘Slave’ empty hard drive for the installation.
The installation wizard will ask you to specify a passphrase that you will use to decrypt your hard drive when you login to Ubuntu.
The encryption wizard will encrypt your ‘home’ folder, just in case if we place our ‘home’ folder outside your Ubuntu installation partition.
That’s it ! Follow the rest of the installation steps and the wizard will install Ubuntu on top of an encrypted partition.
Encrypting a Folder
eCryptfs is a cryptographic file system based on PGP created by Philip Zimmerman on 1991. The great thing about eCryptfs compare to other encryption file system, such as TrueCrypt, is that we do not need to pre-allocate a certain amount of disk space that we want to encrypt.
We can easily install eCryptfs by executing the following command in the console
sudo aptitude install ecryptfs-utils
eCryptfs create a ‘private’ directory in your local drive where eCryptfs encrypts any files that we store in it.
Note: this will setup a hidden private directory:
We should store our sensitive data into the ‘private’ directory to make sure that attackers will not be able to get our data easily. ecryptfs will hide any files that we store in the private folder when it is not mounted.
The private directory will be automatically mounted when we log in to our account. This creates an opportunity for another person to gain access to this private folder when the user leaves the computer. A way to mitigate this problem is to prevent ecryptfs unlocking the private folder when we login by removing the empty file auto-mount which is located in
/.ecryptfs/ and unmount the directory when we’re not using our computer.
Creating a Hidden Encrypted Volume
TrueCrypt is a free Open Source disk encryption utility that works with Windows, Mac, and Linux. It provides on-the-fly encryption and after the drive is encrypted you can continue to use everything like you normally would.
You can download TrueCrypt as Ubuntu deb file from its website. Once downloaded, unpack the archive and double-click on the installer to run the setup. After installation, you will find TrueCrypt from the menu location: Applications > Accessories > TrueCrypt.
Start by creating a volume that we want to encrypt.
A TrueCrypt volume can reside in a file, which is also called container, in a partition or drive.
TrueCrypt gives us an option to create a hidden encrypted volume inside another TrueCrypt encrypted volume.
You should copy sensitive looking files that you do not want to hide to the outer volume. These files act as a decoy when people force you to reveal the outer volume password. You should files that you REALLY want to hide inside the hidden volume, and you should never reveal the encrypted hidden volume.
Now you have to choose the name of the volume file and the location where you want to store the volume file. A new file will be created. If you choose an existing file, it will be overwritten. So give a unique name for your TrueCrypt volume file.
You can choose different levels of encryption. There are several types to choose from and each has its unique qualities…but for most users you will be fine with AES.
set the volume size and make sure you provide enough space for non-encrypted volume space.
TrueCrypt advise us to use at least 20 characters for our password. Choose a password that is easy to remember and not easy to guess.
Move your mouse as randomly as possible within the Volume Creation Wizard window at least for 30 seconds. The longer you move the mouse, the better. This significantly increases the cryptographic strength of the encryption keys (which increases security).
TrueCrypt will automatically mount the encrypted drive as a virtual encrypted disk.
Now we shall setup the hidden volume.
Choose a suitable hard drive format for the hidden volume.
We have the option to make this hidden volume to be compatible with other platforms.
Encryption is just one level of securing our data in our PC, we also need to consider to install other security software such as virus scanner or firewall to protect us from viruses and intruders when we’re online.
Do you need to encrypt a hard drive in Linux? This post will show you how to encrypt a separate partition, a whole hard drive, or just a USB stick. It will work in any Linux distribution.
There are many methods to perform encryption in Linux. In this post, I will show you the encryption method I use the most. It is probably the simplest method to encrypt your data in Linux. It is a command line tool, but there is nothing extraordinary.
Encrypt your hard drive in Linux with LUKS
I usually use LUKS encryption and dm-crypt.
Install the necessary programs
First, you need to install cryptsetup package:
Identify the partition name
Next, make sure the partition you are going to encrypt doesn’t have any important data on it because it will be overwritten during the encryption process.
If your hard drive is brand new, you may need to create a new partition table. If you want to encrypt only part of your hard drive, you also need to re-partition your hard drive into two partitions: one will be encrypted and another one won’t. You can use Gparted for that.
You can also find out the name of your partition with the command lsblk and find the partition you need based on its size.
Encrypt this partition
When the partition you want to encrypt is ready and all the data is backed up into another hard drive, run this command:
Where /dev/sdb1 is the partition you want to encrypt. Next, confirm that you agree to overwrite all the data in this partition.
Next, you will be prompted to type your passphrase. When you type it, you will see nothing. This is normal and due to security reasons. You will need this password to unencrypt the partition. Make sure you memorize it.
Next, open the encrypted partition. This is where you will need to type your passphrase.
Once the partition is opened, the encrypted partition is mapped to /dev/mapper/sdb1 .
Then, create a new filesystem on it:
I also suggest to get rid of reserved space. EXT4 file system reserves some space by default, but you won’t need it if you don’t run your system on this partition. This way you also get more space on the drive:
Now, your partition is encrypted and ready to use.
Test the encrypted partition
Mount it somewhere on your system. /mnt is the most common place to mount partitions.
Let’s create a folder encrypted in it.
And perform the mounting:
Now, you can start placing your files into it. However, you will be able to do that only with sudo because regular users do not have access to this folder.
Let’s change the ownership of this encrypted folder, to give access to regular users:
Now test it by create a file as a regular user without sudo .
You can also create and view encrypted files, from your file manager:
When you finish working with the encrypted partition, unmount it.
Let me remind you that my encrypted partition name is sdb1 , in your case it may be different.
Then, close the mapped device.
Finally, it is safe to disconnect the hard drive from your system.
How to use the encrypted hard
Next time, when you want to use your encrypted drive. You have to connect your hard drive to the system and check its name.
It is sdb1 in my case.
Next, open the encrypted partition with your decryption password:
Now, it is available at /mnt/encrypted . As you can see, the test files we created earlier are there.
When you finished working with this encrypted files, unmount the partition:
In some Linux systems, such Linux Mint in my case, you can also mount the encrypted partition by double-clicking on it in the file manager and entering your passphrase. So, you can avoid the command line hassle.
Conclusion
This way you can encrypt any hard drive, including flash drives. If you encrypt a hard drive that is permanently connected to your system, you can also make it mount automatically on the boot of your system.
For the next read, I recommend you my post about Linux Root Folders.
So, do you use an encrypted partition? What method do you use to encrypt it? Let me know below.
Please consider supporting this project:
- Command Line
- Linux General
- #LUKS
- #command line
- #cryptsetup
- #encryption
- #partition
Comments
Nigel Horne
The mount command fails with:
unknown filesystem type ‘crypto_LUKS’
mbrandizi
Great tutorial, thanks.
Just one addition: this can be used to open the LUKS volume in a non-interactive way:
echo “” | cryptsetup luksOpen /dev/sdb1 sdb1 –
As you can see, the ‘-‘ tells cryptsetup to get the password from the standard input. This is useful for unattended scripts (eg, crontab). Of course, it isn’t secure, if that password is on the same host where the volume is, but it might be reasonable if, for instance, it is (ssh) sent from a remote client that has to backup its local data. Indeed, I’m thinking of using this approach to auto-backup my laptop (where the password can be saved on a secure place like keepass, which is also accessible from scripts).
Thanks mate, this is very helpful and simple to follow
Blaise
Thanks for the tutorial! Could you elaborate on the purpose of the “test1.txt” and “test2.txt” files? It’s not clear what difference using “sudo” has in this case, nor is it clear what this has to do with the drive being encrypted or not.
Average Linux User
You would not be able to create/place files without sudo because you had no permission for a regular user. After you change the ownership with chown , you can place files into encrypted folder without sudo
Use Linux Unified Key Setup to encrypt your thumb drives, external hard drives, and other storage from prying eyes.
Subscribe now
Get the highlights in your inbox every week.
Many people consider hard drives secure because they physically own them. It’s difficult to read the data on a hard drive that you don’t have, and many people think that protecting their computer with a passphrase makes the data on the drive unreadable.
This isn’t always the case, partly because, in some cases, a passphrase serves only to unlock a user session. In other words, you can power on a computer, but because you don’t have its passphrase, you can’t get to the desktop, and so you have no way to open files to look at them.
- Linux commands cheat sheet
- Advanced Linux commands cheat sheet
- Free online course: RHEL Technical Overview
- Linux networking cheat sheet
- SELinux cheat sheet
- Linux common commands cheat sheet
- What are Linux containers?
- Our latest Linux articles
The answer is to place the data on a drive into a digital vault that can’t be opened without information that only you have access to.
Linux Unified Key Setup (LUKS) is a disk-encryption system. It provides a generic key store (and associated metadata and recovery aids) in a dedicated area on a disk with the ability to use multiple passphrases (or key files) to unlock a stored key. It’s designed to be flexible and can even store metadata externally so that it can be integrated with other tools. The result is full-drive encryption, so you can store all of your data confident that it’s safe—even if your drive is separated, either physically or through software, from your computer.
Encrypting during installation
The easiest way to implement full-drive encryption is to select the option during installation. Most modern Linux distributions offer this as an option, so it’s usually a trivial process.
centos8-install-encrypt.jpg
This establishes everything you need: an encrypted drive requiring a passphrase before your system can boot. If the drive is extracted from your computer or accessed from another operating system running on your computer, the drive must be decrypted by LUKS before it can be mounted.
Encrypting external drives
It’s not common to separate an internal hard drive from its computer, but external drives are designed to travel. As technology gets smaller and smaller, it’s easier to put a portable drive on your keychain and carry it around with you every day. The obvious danger, however, is that these are also pretty easy to misplace. I’ve found abandoned drives in the USB ports of hotel lobby computers, business center printers, classrooms, and even a laundromat. Most of these didn’t include personal information, but it’s an easy mistake to make.
You can mitigate against misplacing important data by encrypting your external drives.
LUKS and its frontend cryptsetup provide a way to do this on Linux. As Linux does during installation, you can encrypt the entire drive so that it requires a passphrase to mount it.
How to encrypt an external drive with LUKS
First, you need an empty external drive (or a drive with contents you’re willing to erase). This process overwrites all the data on a drive, so if you have data that you want to keep on the drive, back it up first.
1. Find your drive
I used a small USB thumb drive. To protect you from accidentally erasing data, the drive referenced in this article is located at the imaginary location /dev/sdX . Attach your drive and find its location:
I know that my demo drive is located at /dev/sdX because I recognize its size (1.8GB), and it’s also the last drive I attached (with sda being the first, sdb the second, sdc the third, and so on). The /dev/sdX1 designator means the drive has 1 partition.
If you’re unsure, remove your drive, look at the output of lsblk , and then attach your drive and look at lsblk again.
Make sure you identify the correct drive because encrypting it overwrites everything on it. My drive is not empty, but it contains copies of documents I have copies of elsewhere, so losing this data isn’t significant to me.
2. Clear the drive
To proceed, destroy the drive’s partition table by overwriting the drive’s head with zeros:
This step isn’t strictly necessary, but I like to start with a clean slate.
3. Format your drive for LUKS
The cryptsetup command is a frontend for managing LUKS volumes. The luksFormat subcommand creates a sort of LUKS vault that’s password-protected and can house a secured filesystem.
When you create a LUKS partition, you’re warned about overwriting data and then prompted to create a passphrase for your drive:
4. Open the LUKS volume
Now you have a fully encrypted vault on your drive. Prying eyes, including your own right now, are kept out of this LUKS partition. So to use it, you must open it with your passphrase. Open the LUKS vault with cryptsetup open along with the device location ( /dev/sdX , in my example) and an arbitrary name for your opened vault:
I use vaultdrive in this example, but you can name your vault anything you want, and you can give it a different name every time you open it.
LUKS volumes are opened in a special device location called /dev/mapper . You can list the files there to check that your vault was added:
You can close a LUKS volume at any time using the close subcommand:
This removes the volume from /dev/mapper .
5. Create a filesystem
Now that you have your LUKS volume decrypted and open, you must create a filesystem there to store data in it. In my example, I use XFS, but you can use ext4 or JFS or any filesystem you want:
Mount and unmount a LUKS volume
You can mount a LUKS volume from a terminal with the mount command. Assume you have a directory called /mnt/hd and want to mount your LUKS volume there:
LUKS also integrates into popular Linux desktops. For instance, when I attach an encrypted drive to my workstation running KDE or my laptop running GNOME, my file manager prompts me for a passphrase before it mounts the drive.
It’s good for Windows, but Linux has the above better alternatives. And yes, you should encrypt, especially on a portable computer. If you have any saved passwords stored from browsing, personal information, etc., and you don’t encrypt, you’re taking a big risk.
Should I encrypt my Linux installation?
Should You Encrypt Your Linux Partition? Most Linux distributions make it easy to encrypt your home folder or even entire partitions, without many issues. This is a great option to have if you need your data to be encrypted. In most cases, all you need to do is check a box, and Linux will take care of the rest.
Is it worth encrypting hard drive?
A single encrypted folder is good enough for most people, but a completely encrypted drive provides the strongest protection. Windows can leave bits of encrypted files in places like the swap file. A thief or fence wouldn’t take the time to find them, but a sufficiently skilled, motivated, and well-funded hacker might.
Is full disk encryption necessary?
Simply put, full-disk encryption is overkill for the use case you most likely have. The two encryption configurations we’ve been juxtaposing protect you in different ways. The main difference in the degree of security between them is that file-based encryption only protects your user document and media files.
Does encrypting hard drive slow it down?
Data encryption slows performance and lowers productivity.
“Although mobile computing devices – such as tablets, laptops and smartphones – don’t have the same processing capacities as desktop machines, typically, even their processors can efficiently handle encryption fairly transparently.”
How do I encrypt a drive in Linux?
Disk Encryption in a Linux Environment
- Unmount the file system on the disk. …
- Generate the key to be used by luksFormat . …
- Initialize a LUKS partition and set the initial key. …
- Open the LUKS partition on disk/device and set up a mapping name. …
- Create an ext4 file system on the disk. …
- Set parameters for the ext4 file system.
Does encrypting Ubuntu slow it down?
Encrypting a disk CAN make it slower. For example, if you have an SSD capable of 500mb/sec and then do full disk encryption on it using some crazy long algorithm you might get FAR below that max of 500mb/sec. I’ve attached a quick benchmark from TrueCrypt.
How do I encrypt my entire hard drive?
How to Encrypt Your Hard Drive in Windows 10
- Locate the hard drive you want to encrypt under “This PC” in Windows Explorer.
- Right-click the target drive and choose “Turn on BitLocker.”
- Choose “Enter a Password.”
- Enter a secure password.
Can an encrypted hard drive be hacked?
Encrypted data can be hacked or decrypted with enough time and computing resources, revealing the original content. Hackers prefer to steal encryption keys or intercept data before encryption or after decryption.
What happens when you encrypt your hard drive?
Encryption is the key to protecting the data on your hard drives. You can choose an encryption program that will make it more difficult for the thief to access the information, and prevent anyone who might find your portable drive from accessing it easily.
Does encryption slow down SSD?
No, it doesn’t slow down the “computer” (CPU) at all – it does however slow down the read/write speeds of your hard disk. Depending on the program, and what kind of disk it is, read/write could slow down anything from nothing to 30%.
Does full disk encryption affect performance?
Whole-disk encryption has only minimal impact on the performance of modern computers and hard drives.
What does full disk encryption protect against?
What does full-disk encryption protect against? … Encrypting the entire disk prevents unauthorized access to the data in case it’s lost or stolen. It also protects against malicious tampering of the files contained on the disk.
Is BitLocker a good idea?
BitLocker is actually pretty good. It is nicely integrated into Windows, it does its job well, and it is really simple to operate. As it was designed to “protect the integrity of the operating system,” most who use it implemented it in TPM mode, which requires no user involvement to boot the machine.
Does using BitLocker slow down computer?
BitLocker uses AES encryption with a 128-bit key. … The X25-M G2 is announced at 250 MB/s read bandwidth (that’s what the specs say), so, in “ideal” conditions, BitLocker necessarily involves a bit of a slowdown. However read bandwidth is not that important.
How long does it take to encrypt hard drive?
With an average system, an 80 GB boot disk or partition takes approximately three hours to encrypt using Symantec Drive Encryption (formerly PGP Whole Disk Encryption) when no other applications are running. A very fast system, on the other hand, can easily encrypt such a disk or partition in less than an hour.
Follow MUO
Thinking about encrypting your Linux disk? It’s a wise move, but wait until you’ve considered arguments for and against.
It’s simple to encrypt your home folder and other data on Linux. You can do it during installation, or at anytime using your distro.
But while useful, encrypting your Linux data isn’t necessarily a good idea. Sure, it sounds safe, so how could Linux disk encryption be a bad idea? Let’s look at why you should encrypt your Linux HDD and why you might seek out an alternative.
Should You Encrypt Your Linux Partition?
Most Linux distributions make it easy to encrypt your home folder or even entire partitions, without many issues. This is a great option to have if you need your data to be encrypted. In most cases, all you need to do is check a box, and Linux will take care of the rest.
Unfortunately, some people select it simply because it sounds like a good option to have. While this is clearly true, they don’t think about (or may be unaware of) the consequences. Indeed, some people don’t even know what encryption really is. They just know it’s a security option. This disconnect between understanding the technology can lead to the benefits of disk encryption being overstated and the shortcomings ignored.
It’s smarter to be aware of all the facts before making a decision that irreversibly changes the contents of your hard disk drive.
Reasons to encrypt your Linux disk include:
- Protect personal data from loss or theft
- Prevent the theft of sensitive corporate data
- Block remote surveillance
- Protect sensitive data from third parties
Meanwhile, some negative consequences of disk encryption are:
- Making data recovery more difficult
- Making full system recovery almost impossible
- Hitting system performance
Want to know more? Let’s check all of these in more detail.
4 Reasons to Encrypt Your Linux Drive
We’ll start off with the immediate reasons to encrypt your Linux data. This might be specific files, one or more partitions, or even the entire drive.
1. Protect Personal Data From Loss or Theft
For standard users, especially laptop owners, this is the key point. You don’t want to risk personal data and potentially access to emails and cloud accounts, if your device is stolen.
Encrypting your hard disk will block access to these items. Whether files, partitions, or the full disk is encrypted, the contents will be meaningless to anyone without the encryption key.
2. Prevent Theft of Sensitive Corporate Data
Similarly, if you use your computer for work, encryption is a smart option. Whether a laptop computer or a desktop, the device should have encryption enabled. The industry you work in can influence how important this is (e.g. protecting patient data in healthcare).
However, it is smart to just use encryption across the board in the workplace. Protecting data from corporate espionage or whaling expeditions is smart.
3. Block Remote Surveillance
Full disk encryption of your Linux system can also frustrate remote surveillance. A hacker with access to your computer will not be able to read encrypted data. A government agency charged with monitoring your data will be unable to open your files.
4. Protect Sensitive Data From Third Parties
If you manage data for someone else (whether a client, or someone in danger), disk encryption is wise. It protects them from risk, while getting you off the hook if the data is lost or stolen.
Remember: if the data remains encrypted, it cannot be read. Beyond the astronomically unlikely chance that the encryption is broken, data should be secure.
3 Arguments Against Linux Disk Encryption
Disk encryption is a great idea, but be sure you know and understand the implications.
1. Disk Encryption Makes Recovering Data Harder
Encrypting your data seems like a smart option. Without decryption (linked to your account password), no one can access your data. Even if the device is stolen, your hard drive cannot be read without the decryption key.
But what if something in your system has screwed up? Whether it’s the operating system or another hardware component, you’ll probably want to move the data somewhere safe.
For unencrypted data this can be easily done by running (at the minimum) a Linux LiveCD on any other computer. Simply connect the hard drive to that computer and start moving your data.
But with encrypted data, it’s not as easy as that.
2. System Recovery Is Impossible With Disk Encryption
Meanwhile, if your entire Linux partition is encrypted it will be tougher recovering your system when needed. For example, if your system loses power at a critical point, you’ll need to run a recovery disc. It’s the only way to get things back to normal.
Performing recovery on an encrypted Linux system will be even harder. Without the decryption key, unless you have an unencrypted disk image, you’re on a hiding to nothing.
3. Encrypting Your Hard Drive Impacts Performance
Another item to note is that encryption may not be the best performance option for very low-powered devices. While plenty of devices are powerful enough to deal with encryption with negligible performance impact, older hardware is not.
Installing Linux on old netbooks and other low-power devices is fine. But do it without encryption. After all, netbooks are slow enough already. The idea is to be productive with these low-spec devices, rather than sit around waiting for them.
Linux Disk Encryption Is Your Shout
As always, what you end up doing is completely up to you. If you feel that you need to encrypt your entire home folder or even your whole partition, go ahead. So long as you’re aware of what might be facing you in the event of a problem.
On the other hand, if you prefer to leave your drive unencrypted and secure your data in other ways, you can. Just be confident your data is as secure as promised.
Ditch the default Python editor and don one of these shiny IDEs. Your code will thank you.
Deputy Editor for Security, Linux, DIY, Programming, and Tech Explained, and Really Useful Podcast producer, with extensive experience in desktop and software support. A contributor to Linux Format magazine, Christian is a Raspberry Pi tinkerer, Lego lover and retro gaming fan.
Subscribe to our newsletter
Join our newsletter for tech tips, reviews, free ebooks, and exclusive deals!
NOTE: Your company may have alternate specific guidance for how you should encrypt your hard drive – please check with your IT and compliance teams.
HERE’S HOW
Open System Preferences, then click on Security & Privacy
Click on the FileVault tab
If FileVault is not turned on, click the “Turn On FileVault…” button
You may need to click the lock in the lower left corner to make changes
You should see the following if FileVault is enabled:
On Windows Professional 10:
Locate the hard drive you want to encrypt under “This PC” in Windows Explorer.
Right-click the target drive and choose “Turn on BitLocker.”
Choose “Enter a Password.”
Enter a secure password.
Choose “How to Enable Your Recovery Key” which you’ll use to access your drive if you lose your password.
Choose “Encrypt Entire Drive.” This option is more secure and encrypts files you marked for deletion.
Click “Start Encrypting” to begin the encryption process.
NOTE 1: BitLocker is not available for Windows Home Edition.
NOTE 2: You will need to manually upload evidence of disk encryption on Windows when using the Drata agent. See this article for more details.
On Ubuntu Linux:
NOTE: You will need to manually upload evidence of disk encryption on Linux when using the Drata agent. See this article for more details.
There are lots of Linux servers out there – sufficiently many that it’s impossible to give the precise number, and difficult even to come up with a good approximation.
But we’re unlikely to offend anyone if we say that at least 20%, probably 40%, and possibly more than 50% of the internet’s servers run some flavour of Linux.
As a result, cybercrooks have learned how to hack into Linux servers on an industrial scale in order to steal both storage space and network bandwidth.
With these hacked servers, they push malware, spam, scams and phishing campaigns onto users worldwide.
Of course, the vast majority of the victims who get attacked or infected via compromised servers are running Windows, simply because the vast majority of end users are running Windows.
If you run a Linux desktop, life can be a lot quieter.
Part of that is being in a small minority, with Linux probably running on only about 2% of desktop computers worldwide.
Being in a small minority means you haven’t yet attracted much attention from cybercriminals, who are making huge amounts of money from the Windows ecosystem already.
But is that enough to consider yourself safe?
Linux malware does exist and has occasionally spread extensively in the wild; Linux users do get phished; Linux laptops do get lost, or stolen or hacked; hard disks do get removed from Linux computers and sold without being wiped – and any of these could put you, your privacy, or even your identity, at risk.
So here are five easy steps to enhance your Linux security.
1. Choose Full Disk Encryption (FDE)
No matter which operating system you are using, we recommend that you encrypt your entire hard disk.
If your laptop is lost or stolen, using a simple login password won’t protect your data: a thief can just boot into Linux from a USB key and read all your data off without a password.
By encrypting your hard drive, you ensure your data remains secure, because the thief won’t be able to read anything without the FDE password.
The advantage of FDE over encrypting just your home folder and the files in it is that you no longer have to worry about temporary files, swap files or other directories where important files might end up without you realising it.
On any fairly recent computer, you’re unlikely to notice, or even to be able to measure, a slowdown in day-to-day use due to encrypting everything.
On Ubuntu and Fedora, as in many other Linux distributions (distros for short), full disk encryption is available right at install time.
You can easily enable it during the installation by selecting Encrypt the new Ubuntu installation for security:
And, of course, remember to pick a proper password!
2. Keep your software up-to-date
Again, no matter which operating system you are using, you should always keep both your operating system and your applications, such as web browsers, PDF readers and video players, up to date.
Most Linux distros make this easy.
On Ubuntu, by default, security updates are installed automatically.
You can double-check this at System Settings | Software & Updates | Updates.
Make sure the Important security updates option is turned on:
3. Learn how to use Linux’s firewall
The Linux kernel includes a firewall component called iptables, which gives you a powerful way to manage network traffic and keep out many sorts of cyberattack.
On Ubuntu you will also have an application called Uncomplicated Firewall (UFW), a frontend program that simplifies setting up iptables.
By default UFW is disabled, but you can turn it on from a command prompt by doing:
To learn more about iptables and what it can do, you might also want to try a graphical configuration tool such as GUFW or UFW Frontends.
On Fedora you will find FirewallD, an alternative firewall management toolkit that is enabled by default.
A graphical user interface for FirewallD, called firewall-config, is available; you can install it from a command prompt with:
4. Tighten up security in your browser
The browser is the way in for many current cyberthreats, whether you use Mozilla Firefox, Google Chrome, Opera or another browser.
Many free extensions are available to improve the security of your browser, and your privacy as well. Among others, you may want to consider the following:
5. Use anti-virus software
We saved this one until last because it has long been a bone of contention with a vocal minority of Linux faithful.
Some people will tell you that it’s pointless installing an anti-virus software on a Linux-based operating system.
Half of the argument is that most of the malware you will detect on a Linux computer will be for Windows, and why should you be responsible for that?
The obvious answer is, “Why not? What if you pass an infected file onto someone else and thus make yourself part of the problem rather than the solution?”
The other half of the argument is that malware on Linux desktops is rare enough that you might as well pretend it doesn’t exist at all.
My personal opinion is that if you feel safe just because you think the risk of a breach is low, then attackers have already outsmarted you.
Tux (the Linux penguin) by Larry Ewing, Simon Budig and Anja Gerwinski, downloaded courtesy of Wikimedia Commons.
Follow @NakedSecurity on Twitter for the latest computer security news.
Follow @NakedSecurity on Instagram for exclusive pics, gifs, vids and LOLs!
- 1 For best practice to protect the data on your laptop, you should encrypt the information to protect it from unauthorised access. To determine if your disk encryption is enabled, please follow these steps below.
- 2 Windows laptops
- 3 macOS laptops
For best practice to protect the data on your laptop, you should encrypt the information to protect it from unauthorised access. To determine if your disk encryption is enabled, please follow these steps below.
Windows laptops
Device encryption is available on all editions of Windows 10, but BitLocker encryption is available only on Windows 10 Pro, Enterprise or Education versions. Windows 10 Home does not support BitLocker, but you can still use device encryption as long as your device (laptop) meets the hardware requirements.
Check the version of your Windows operating system
Click on the Start Menu at the bottom left hand corner of the screen:
In the Type here to search box, type “system information” and click on the System Information tab to display the version of Windows used on your device:
Check if your device is encrypted (Windows 10 Home edition)
Click on the Start Menu at the bottom left hand corner of the screen:
Click on the Settings cogwheel icon:
Click on Update & Security:
In the left-hand column Click on Device encryption:
If you see the message Device encryption is on with the option to Turn off, your hard drive IS encrypted:
If the encryption is NOT turned on, click on Turn on to encrypt your device and follow the instructions.
Check if your device is encrypted (Windows 10 Pro/Enterprise/Education editions)
In Windows Explorer in the left hand column, click on This PC and on the right hand side you should see a padlock icon on the drives that are encrypted.
Highlight and right-click on the drive you want to verify the “BitLocker Options”. If you see the message Encryption on, your hard drive IS encrypted:
If your drive does not have the padlock icon, it is NOT encrypted. Right-click on the drive and select Turn on BitLocker and follow the on-screen instructions.
macOS laptops
FileVault 2 is available on macOS Lion or later.
Check the version of your macOS operating system
Click on the Apple icon on the top left-hand corner of the screen:
Click on About This Mac to display information about the macOS version:
Check if your macOS disk is encrypted
Click on System Preferences and then on the Security and Privacy icon:
If you see the message FileVault is turned on for the disk “Macintosh HD” with the option to Turn off FileVault, this means that your disk IS encrypted:
If you see the message “Filevault is turned off. “, this means that your disk is NOT encrypted. Please click on Turn on FileVault to encrypt your disk and follow the on-screen instructions.
Before starting full disk encryption on a computer, you are advised to make sure that the computer is not infected. To do so, start the Full Scan or Critical Areas Scan task. Performing full disk encryption on a computer that is infected by a rootkit may cause the computer to become inoperable.
To perform full disk encryption using Kaspersky Disk Encryption technology:
- Open the Kaspersky Security Center Administration Console.
- In the Managed devices folder in the Administration Console tree, open the folder with the name of the administration group for which you want to configure full disk encryption.
- In the workspace, select the Policies tab.
- Select the necessary policy.
- Open the Properties :
window by using one of the following methods:
- In the context menu of the policy, select Properties .
- Click the Configure policy link located in the right part of the Administration Console workspace.
Kaspersky Disk Encryption technology cannot be used if the computer has hard drives that were encrypted by BitLocker.
In the Encryption mode drop-down list, select Encrypt all hard drives .
If the computer has several operating systems installed, after encrypting all hard drives you will be able to load only the operating system that has the application installed.
If you need to exclude some of the hard drives from encryption, create a list of such hard drives.
Select one of the following encryption methods:
- If you want to apply encryption only to those hard drive sectors that are occupied by files, select the Encrypt used disk space only check box.
If you are applying encryption on a drive that is already in use, it is recommended to encrypt the entire drive. This ensures that all data is protected – even deleted data that might still contain retrievable information. The Encrypt used disk space only function is recommended for new drives that have not been previously used.
If you want to apply encryption to the entire hard drive, clear the Encrypt used disk space only check box.
This function is applicable only to unencrypted devices. If a device was previously encrypted using the Encrypt used disk space only function, after applying a policy in Encrypt all hard drives mode, sectors that are not occupied by files will still not be encrypted.
If a hardware incompatibility problem was encountered during encryption of the computer, you can select the Use Legacy USB Support check box to enable support for USB devices during the initial computer startup phase in BIOS.
Enabling / disabling Legacy USB Support does not affect support for USB devices after the operating system is started.
When Legacy USB Support is enabled, Authentication Agent does not support operations with USB tokens if the computer is operating in BIOS mode. It is recommended to use this option only when there is a hardware compatibility issue and only for those computers on which the problem occurred.
For details on applying a Kaspersky Security Center policy, please refer to the Kaspersky Security Center Help Guide.
When we talk about encryption, often we’re referring to software encryption that requires a user’s password as an encryption key. However, this isn’t the only type of encryption. This guide to the benefits of hard disk encryption software will define and discuss encryption and how it can aid Linux disk encryption, Mac disk encryption, and Windows 10 disk encryption. Hard disk encryption software can improve your security—both internally and for your customers—helping save you time, mitigate liability, and reduce the impact of human error.
Related Product
N-central
Manage complex networks with RMM that offers strong automation, visibility, and security.
What Is disk encryption?
Disk encryption software prevents a disk drive, like a hard drive in a portable USB storage device or laptop, from booting up unless the user inputs the correct authentication data. The booting up process for an operating system involves the first section of the disk—the master boot record—informing the system of where to read the first file, which initiates the loading of the operating system. Without encryption, no special instructions are required to interpret the contents of the disk. By default, files are written in plain text.
When you use disk encryption software, this process is modified. The contents of the disk (except for the master boot record) are encrypted using a modern symmetric cipher accessible via a secret key. The master boot record is modified so that it loads this system, which validates the authentication data from the user. If the authentication process is successful, the encryption key is unlocked.
This system, which varies between different implementations, stores the master key for the device. Authentication information might be a password, a public key-based token, or a fingerprint scan. Once the valid authentication data is read, the master key is decrypted. The master key then remains in the computer’s memory while it’s powered-on. This allows the operating system to first read the disk to boot up, as well as read any other disk contents the user requests while using the computer.
The benefits of hard disk encryption software
1. SECURING DATA FROM HACKERS
Volume level disk encryption helps protect you and your customers from data theft or accidental loss, by rendering data stored on hard drives unreadable when an unauthorized user tries to gain access. Hard disk encryption software makes it very for data to be accessed or stolen by hackers. Even if a hacker were to remove the disk drive from the computer, the information stored on the drive would remain encrypted and recovery would be impossible. As such, disk encryption software provides an effective way of securing your data against cyberattacks.
2. ELIMINATING THE RISK OF HUMAN ERROR
If the security of your data is subject to manual encryption methods, mistakes will inevitably occur. Mistakes of this nature—such as data loss—could result in significant repercussions, including legal liability, damaged reputation, and financial loss. By using automatic encryption methods rather than manual processes, you remove the element of human labor that introduces an additional layer of risk.
3. ELIMINATING THE RISK OF DATA LEAKS
A data leak refers to sensitive data being accidentally exposed. This might be a physical exposure, a vulnerability that could be exploited over the internet, or an exposure in any other form that would result in data falling into the hands of unauthorized individuals. Disk encryption software helps eliminate the risk of data leaks. For example, if a hard drive or laptop were to go missing, disk encryption would help ensure someone couldn’t read the sensitive data stored on the device.
4. MITIGATING THE LIKELIHOOD OF LIABILITY ISSUES ARISING
Disk encryption is ideally suited to organizations that handle data considered to be a critical asset, or which is governed by compliance regulations—for example, GDPR. Wherever there is a risk of data loss, disk encryption software can help protect your company from potential liability issues. This is an especially important consideration for MSPs, as you’re likely to be exposed to higher liability risks due to your data management responsibility for multiple customers.
5. SAVING TIME
Manual encryption methods are extremely time-consuming and significantly less efficient than using disk encryption software. To achieve high-level security with minimal effort, as MSPs should always aim to do, disk encryption software is an ideal solution.
How all-in-one software can help
SolarWinds® N-central® is an all-in-one remote management and monitoring tool that includes highly advanced and user-friendly disk encryption software. As an all-in-one solution, N-central is an ideal tool for busy MSPs, as it helps eliminate the need to implement multiple separate security, management, and monitoring platforms. This is a multi-platform tool providing Linux disk encryption, Mac disk encryption, and Windows 10 disk encryption.
The N-central tool features a security manager tool, which includes integrated disk encryption functionality. This gives you three security options, which are:
- Trusted Platform Module (TPM)—This is a hardware-level security module available on certain computers. When TPM is enabled, the user doesn’t need to enter a password when booting their computer. Instead, they’re presented with the Windows login screen and no password is necessary.
- Trusted Platform Module and PIN—With TPM and PIN used together, the user must input a PIN to unlock the disk and access the login screen. This is the most secure method of encrypting and safeguarding data. This disk encryption security option is recommended by Microsoft.
- Password—This option is the default security setting when a system doesn’t have TPM available, or when it’s not enabled. With this security option, the user is prompted to enter a password when they log into their computer. If the password is correct, the disk is unlocked and the user can proceed to the Windows login screen.
N-central offers an array of other features, including powerful automation that helps you onboard, configure, or patch hundreds of devices with ease. The program’s advanced security solutions, which also include endpoint detection and response, help you to protect your customers at every level—against even the most sophisticated threats. For MSPs interested in learning more, a 30-day free trial of SolarWinds N-central is available.
Ubuntu Core 20 uses full disk encryption (FDE) whenever the hardware allows, protecting both the confidentiality and integrity of a device’s data when there’s physical access to a device, or after a device has been lost or stolen.
Built-in FDE support requires both UEFI Secure Boot and TPM 2.0 (Trusted Platform Module) support, but its implementation in Ubuntu Core is generic and widely compatible to help support a range of hardware. TPM-based FDE seals the FDE secret key to the full EFI state, including the kernel command line, which is subsequently unsealed by the initrd code in the secure-boot protected kernel.efi at boot time.
The following factors affect how a device is encrypted:
- Storage layouts: the potential partitions created on the device
- Disabling encryption: an optional parameter that can disable encryption
- Model grade: interacts with storage-safety to set the device constraints
For a non-standard (non-UEFI+TPM platform) FDE platform, such as a Raspberry Pi or other ARM devices, implementation is board-specific and will typically involve creating custom gadget and kernel snaps. UC20, however, does provide a helper mechanism, via a hook interface, to ensure the integrity of any subsequently executed or accessed data. See UC20 full-disk-encryption hook interface for further details.
Storage layouts
The layout of the generated image used to install Ubuntu Core, and the resultant storage on the device, is described by the gadget snap and its associated gadget.yaml.
Ubuntu Core 20 typically uses the following storage partitions:
- ubuntu-seed (role: system-seed; read-only, ext4 or typically vfat)
- ubuntu-boot (role: system-boot; read-only, ext4 or vfat):
- ubuntu-save (role: system-save; writable, ext4, encrypted)
- ubuntu-data (role: system-data; writable, ext4, encrypted)
ubuntu-save is mandatory on an encrypted system. The initramfs bootstrapped from ubuntu-boot is responsible for decrypting both the ubuntu-save and ubuntu-data partitions.
The system boot process:
- verifies the bootloaders and kernel signatures
- measures the above and the kernel command line with the TPM
- on-top of the above trusted set, the snapd initrd code measures the snap device model
- snapd then separately verifies other snaps with their assertions as needed
When run normally, the snap content comes from snaps in the encrypted data partition, with the exception of the kernel image which is loaded from the system boot partition via secure boot. In any case the unsealing of the disk encryption key(s) is tied to the correct TPM boot measurements.
For further details on how Ubuntu Core 20 uses these partitions, what they contain, and how they boot, see Storage layout.
Disabling encryption
It is sometimes desirable to install Ubuntu Core 20 without encryption, even when the device hardware supports it.
This option is provided by the “storage-safety” setting in the model assertion used to build the installable image. It can be set to one of the following:
- prefer-unencrypted: do not encrypt by default, even if the device supports encryption.
- prefer-encrypted: do encrypt if the hardware supports it.
- encrypted: ensure encryption is used and fail if the device does not support it.
See Creating a bespoke image for further details on building an image from a model assertion.
Model grade
The grade option in the model assertion is used to set the constraints for the device. It can be one of the following:
- dangerous: relax some of the constraints here (mandatory snap id for example), and should allow for the use of unasserted snaps, devmode snaps, or the presence of extra snaps in the recovery system. These relaxations are meant for development and not for production system use as they weaken the system security.
- signed (default): no unasserted (unsigned) snaps or snaps not mentioned in the model can appear or be used in the recovery system.
- secured: same properties as signed plus it is mandatory for the device to use full disk encryption and secure boot.
The snap model command can be used to view the currently running model declaration, including its grade and storage-safety values:
The values of both a model’s grade and the storage-safety option influence whether a device is encrypted, unencrypted, or generates an error, as shown in the tables below:
With hardware support
| grade ↓ / safety → | unset | encrypted | prefer-encrypted | prefer-unencrypted |
|---|---|---|---|---|
| dangerous | encrypted | encrypted | encrypted | unencrypted |
| signed | encrypted | encrypted | encrypted | unencrypted |
| secured | encrypted | encrypted | encrypted | invalid |
Without hardware support
| grade ↓ / safety → | unset | encrypted | prefer-encrypted | prefer-unencrypted |
|---|---|---|---|---|
| dangerous | unencrypted | error output | unencrypted | unencrypted |
| signed | unencrypted | error output | unencrypted | unencrypted |
| secured | error output | error output | error output | invalid |
Note : grade:secured is the same as grade:signed and storage-safety:encrypted .
storage-safety:prefer-encrypted is the same as unset
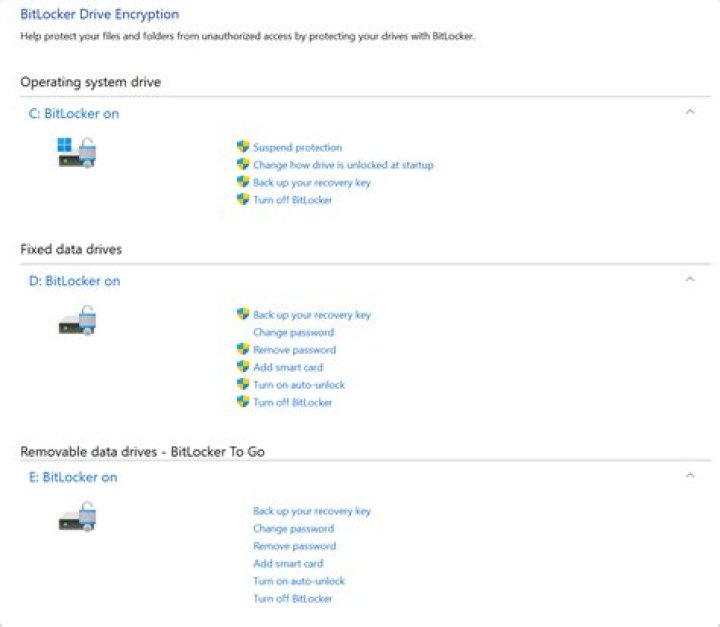
All staff [email protected] hard drives (laptops and desktops) should be encrypted using BitLocker Drive Encryption technology. Furthermore, any loaned or personal devices (BYOD) which will be connected to the UCL network or used to conduct UCL business activities are to be encrypted before use. Bitlocker encryption is good enough to meet GDPR requirements as long as the devices are always locked when unattended. If a device with Bitlocker enabled, is left unlocked, anyone with access to it can view data stored on the device. ISG strongly recommend that users do not set their devices to the sleep mode as it does not completely lock the device.
What is BitLocker?
BitLocker is Microsoft’s easy-to-use, proprietary encryption program for Windows that can encrypt your entire drive as well as help protect against unauthorized changes to your system such as firmware-level malware.
BitLocker is available to anyone who has a machine running Windows Vista or 7 Ultimate, Windows Vista or 7 Enterprise, Windows 8.1 Pro, Windows 8.1 Enterprise, or Windows 10 Pro. The Bitlocker enterprise edition is available to all [email protected] and laptops.
How do I enable Bitlocker on a windows machine?
To enable BitLocker encryption on windows desktops and laptops, simply follow these steps:
Select [Start Menu]
Type “Bitlocker” into the search box
Select [Bitlocker Drive Encryption]
Click on [Turn on Bitlocker]
1. Open Windows’ Control Panel, type BitLocker into the search box in the upper-right corner, and press Enter.
2. Next, click Manage BitLocker, and on the next screen click “Turn on BitLocker”.
3. Now BitLocker will check your PC’s configuration to make sure your device supports Microsoft’s encryption method.
How do I enable Bitlocker encryption for Windows 10?
For Windows 10 build 1511 or later, there are options to choose your encryption mode: new or compatible. If you’re encrypting your on-board storage drive, then choose new. The compatible mode is mostly for removable drives that will be used with older versions of Windows that do not have the “new” encryption mode.
Click on the box next to Run BitLocker system check so that Windows will run a system check before encrypting your drive.
Once the box is checked, click Continue. and nothing happen
Select [Start Menu]
Type “Bitlocker” into the search box
Select [Bitlocker Drive Encryption]
Click on [Turn on Bitlocker]
How do I check the Bitlocker status it has been enabled?
Using the BitLocker Drive Encryption application to check Bitlocker status.
You can check the BitLocker status of a machine using the BitLocker Drive Encryption application, which is in Control Panel
The BitLocker Drive Encryption application displays the status of the drives attached to the system e.g. C: is encrypted, E: is not encrypted, F: is in the process of encrypting.
How do I enable encryption on a Mac?
The new Mac computers with T2 security chip have a built in encryption of your Home folder. There is also an option of using the Disk Utility tool to create an encrypted disk image to store encrypted files. In addition users are advised to turn on FileVault for additional security which requires a password to decrypt data.
How do I turn on FileVault?
You can turn on FileVault by following the instructions on this link:
Encryption For Linux
Full disk encryption on Linux depends on which Linux distribution you are using, see the links below for instructions for some popular Linux distributions:
Encrypting a hard drive partition is a great way to hold a lot of sensitive data without needing to go through the tedious process of using a tool like GnuPG, VeraCrypt, and others, to individually lock files and folders. Better yet, encrypting an entire drive ensures that your data will always be safe, even if you forget to take steps to make your data private.
When it comes to encrypting hard drive partitions on Linux, no application is more straightforward than Gnome Disk Utility. Out of all of tools that can encrypt hard drive partitions on Linux, it manages to be the easiest to understand for average users. And it has some of the best options for disk encryption, despite being as basic as it is, compared to tools like Gparted or KDE Partition manager.
Install Gnome Disk Utility
Before talking about how you can use the Gnome Disk Utility application to lock up partitions or entire hard drives on your Linux PC, we need to go over how to install it. Mainly because not every Linux operating system comes with it by default.
To install the Gnome Disk Utility application on Linux, open up a terminal window by pressing Ctrl + Alt + T or Ctrl + Shift + T on the keyboard. Then, follow the instructions that correspond to the Linux OS you currently use.
Ubuntu
Debian
Arch Linux
Fedora
OpenSUSE
Generic Linux
The Gnome Disk Utility application is a favorite to include with most Linux distribution manufacturers, so, many users — even ones on obscure distributions have it in their software sources.
To get Gnome Disk Utility, open up a terminal and search for “gnome-disk-utility” or “gnome disks.” Then, try to install it the way you’d typically do on your computer. Alternatively, you can grab the source code for the application here.
Lock hard drive partitions
The Gnome Disks application supports encryption with the help of LUKS. In a previous article, I went over how to use this feature to lock a USB disk. This feature can also be used to lock hard drive partitions on Linux, or even entire drives.
Back up your data
Encrypting a USB drive is easy because most people don’t keep that much data on it. Hard drives, however, tend to hold a ton of data. So, if you plan to lock a drive or specific partition, it’s a good idea first to back it up, as the encryption process requires formatting.
To start, mount the drive on Linux. You can easily do this by opening up your file manager. Then, look at the “Devices” section of the file manager for your drive or partition and double-click on it to mount.
Once the drive is mounted, begin copying your data to somewhere safe like an external drive or a different hard drive. When done, go back to the “Devices” section of the file manager and right-click on the drive. Then, select “Unmount.”
Reformatting
As useful as it would be to be able to retroactively convert a non-encrypted hard drive into an encrypted one without needing to reformat, it isn’t possible. To reformat, open up the Gnome Disks app on your computer. Then, look to the sidebar of the program for the hard drive you want to work with and select it from the mouse. From there, click the menu icon on the right side of the app, and click the “Format Disk” option inside.
Ensure it’s set to GPT if you want it to work with modern computers. Otherwise, change it to MBR in the “Partitioning menu.” When everything looks OK, click the “Format” button to delete everything from your hard drive.
Set up a separate locked partition
Don’t want the entire space of the drive to be locked? If so, set up a dedicated encrypted Linux partition by following these steps.
Step 1: Click the + sign to create a new partition.
Step 2: Use the slider to create a partition. Be sure not to use the entire size of the hard drive. Then, click “Next.”
Step 3: On the next page in Gnome Disks, use the UI and set the label of the new partition.
Step 4: Move down to “type” and choose “Internal Disk for Linux systems only.” Also, check the box next to “Password protect volume.”
Step 5: Click the “Next” button to move on to the password creation page. Then, use the UI to set a memorable passcode.
Step 6: Select the “Create” button to make your new encrypted partition.
Step 7: Go back to hard drive in Gnome Disks, click the + sign again and create a second, unecrypted partition to fill out the rest of the drive space.
Lock the entire hard drive
Step 1: Click the + sign to create a new partition.
Step 2: Use the slider to create a partition that uses all of the free space on the drive, and click “Next” to continue.
Step 3: Write the name of the volume in the name box. Then, choose “Internal Disk for Linux systems only,” and “Password protects volume.”
Step 4: Select the “Next” button to move to the password creation page.
Step 5: On the password page, set a secure, memorable passcode for your new partition. Then, click the “Create” button to make your new encrypted partition.
We have explaned in some simple steps, how to encrypt your Radboud-laptop yourself. Also, you’ll find information on other operating systems (Mac, Linux and Windows education or home edition) and encryption software.
Encrypt your Radboud laptop in 9 steps
Before you get started, make sure your laptop is plugged in and that you have a USB-stick handy. And preserve some time – it may take a while for your laptop to get encrypted.
- Right click on the C drive and clik on [Turn on BitLocker].
- Click [Next] three times in a row.
- Choose an option for saving the key. Here, choose ‘USB-stick’ (and save it to your computer as well, until you’ve brought the key to the Service Desk).
- Click [Next] and [Continue] if you’re ready to encrypt the drive.
- You get a message that your computer must be restarted. Click on [Restart]. After that, your C drive is encrypted.
- Repeat step 1 for the D drive.
- Check ‘Automatically Unlock this drive on this computer’ and click [Next].
- Save this key on your USB-stick as well (make sure both keys are recognisable as such).
- Click [Start encrypting].
Saving the key
Now your C and D drive are encrypted, all you have to do is drop by the ICT Service Desk to register your keys. Please do this as soon as possible and bring both your laptop and the USB-stick. In addition, you can save the key by, for example, e-mailing it to yourself or save it in a password vault like Keepass.
Other operating systems and encryption software
How you exactly encrypt your laptop, depends on the (version of the) operating system on your computer. Roughly, these encryption programmes match with these types of laptops:
| BitLocker | VeraCrypt | Filevault |
|---|---|---|
| Windows | x | x |
| Mac | x | x |
| Linux | x |
BitLocker
BitLocker is standard software on the ‘educational-version’ of Windows – but not on the ‘home-versie’. Via Surfspot you can upgrade home to educational.
VeraCrypt
VeraCrypt is free software that allows you to encrypt your hard drive. VeraCrypt is for the advanced user. If you are not an advanced user, choose Bitlocker (and thus the upgrade mentioned above).
- Download VeraCrypt.
- Start VeraCrypt en follow the instructions. There is als a manual available on this page.
Filevault
The encryption programme Filevault is normally available on the Mac.
- Open ‘System Preferences’ on your Mac.
- Go to ‘Security and privacy’ and open het tab ‘Filevault’.
- Turn on Filevault and follow the instructions.
Ubuntu Linux has quickly become the most popular GNU/Linux distribution in use on workstation computers. Ubuntu is user-friendly, doesn’t cost a dime, and is powered by open source software. One of Ubuntu’s best features is full disk encryption, an important security and privacy feature that keeps data on your hard drive scrambled in case it’s lost, seized, stolen, or if you choose to sell or give away your computer in the future.
Right now most users don’t even realize that Ubuntu offers full disk encryption because the option is not included in the popular default Live CD installer. Instead you have to use the text-based alternate CD to install Ubuntu with disk encryption. If we ever hope to make it common practice for laptop users to encrypt their drives, encryption needs to be in the default installation – not some special alternate installation.
We can do something about this! Ubuntu Brainstorm is a simple way to contribute ideas and to have the community to vote on them. Ideas that get lots of votes gain the attention of the developers. If you care about getting full disk encryption built-in to the Ubuntu Live CD installer, please create an Ubuntu Brainstorm account and vote on this idea.
Why encrypt your hard drive?
Encrypting your hard drive protects your privacy and your data in case your computer is lost, seized, stolen, or otherwise ends up in someone else’s hands. Police are unlikely to access your encrypted data without your cooperation or a court order, so using disk encryption makes it much more difficult for them to violate your Fourth Amendment rights that protect you from unreasonable search and seizure.
In addition to being simpler and easier than only encrypting documents that you consider sensitive, full disk encryption protects you in a variety of ways that partial encryption does not. Sensitive data ends up on your hard drive that you might not think about or realize is there, including your browser history, cookies, and saved passwords. Full disk encryption also prevents attackers from changing operating system or application files to compromise your security. Federal government laptops have been encrypted since 2006. Shouldn’t yours be as well?
There are some attacks against disk encryption, such as the cold boot attack and the evil maid attack. These require special conditions, are hard to pull off, and are difficult for law enforcement to justify doing without probable cause. It’s possible, though inconvenient, to protect yourself from both of these. You can also protect yourself against the brute-force attack by choosing a good, long passphrase.
How do I encrypt my hard drive with Ubuntu now?
In the meantime, if you want to use full disk encryption in Ubuntu download a copy of the alternate installer CD. Boot to it and follow the instructions. When you get to the “Partition disks” step choose “Guided – Use entire disk and set up encrypted LVM”, and type your new encryption passphrase twice. When the installation is done your computer will reboot and you’ll need to type your passphrase to unlock your hard drive before Ubuntu can boot. It’s more difficult to dual-boot with Windows while using encrypted Ubuntu partitions, but there’s no reason why this shouldn’t be a one-click option as well.
Ready to help make encryption the default? Head over to Ubuntu Brainstorm and vote.
Restic windows backup. effectively, only transferring the parts that actually changed in the files you back up none Configuration file. to many different storage types, including self-hosted and online services. Velero Service Principal must be owner of the AKS Node Resource Group. It supports the three major operating systems (Linux, macOS, Windows) and a few smaller ones (FreeBSD, OpenBSD). Jerod Santo. It aims to be easy, fast, verifiable, secure, efficient, and free. **Restic Backup (now using for PC / web server backups) ** I’ve been using Restic Backup for a couple of years now. Get alerts when your restic backup have failed, or didn’t finish on time. With this tool, you can create bash scripts or cron jobs to suit your Linux backup needs And when I try to create the same, restic confirms there is already a config/repo there: C:\restic> . Of course, using that path, a Windows program won’t find the target, but it should be able to just backup the link contents. 12. restic backup /. [email protected]:
$ velero backup create my-mysql-backup –include-namespaces default Backup request “my-mysql-backup” submitted successfully. – mark42inbound Feb 6 ’19 at 6:38. Protecting and backing up your VMs is an essential part of ensuring long-term stability for your infrastructure. Restic is certified for use with Wasabi. Step 1 – Configure mc client. If a tree blob cannot be loaded, restic now warns about this problem with the backup repository. rdiff-backup is reverse differential backup. It supports backends for storing backups natively, including on the local directory, sftp server (via SSH), HTTP REST server (protocol rest (Scroll down to the very bottom of the page. Restic – A fast, secure and efficient backup application. for the backup command: $. The software can backup your entire system, whole drives … restic REST server. Not as space efficient as zpaq but twice as fast. It is available in the attached zip: restic-backup-windows-vss. For example, we expect that the garbage collection process (restic prune) will be an order of magnitude faster for almost all users. It is written in Go. I lost the windows where it shows each layer and the tab restic backs up to repositories. Note The MaxShadowCopies setting is supported on Windows Server 2003 or later. The following may also be of interest to Linux users, as Backblaze doesn’t offer a personal backup system for linux OS. The command is fairly simple. # that are in use to be backed up. It’s block based and efficient with disk / network. Default value: [] backup_path. The above command automatically creates a snapshot of the
Azure Disk encryption can be applied to both Linux and Windows virtual machines, as well as to virtual machine scale sets.
Linux virtual machines
The following articles provide guidance for encrypting Linux virtual machines.
Current version of Azure Disk Encryption
- Overview of Azure Disk Encryption for Linux virtual machines
- Azure Disk Encryption scenarios on Linux VMs
- Create and encrypt a Linux VM with Azure CLI
- Create and encrypt a Linux VM with Azure PowerShell
- Create and encrypt a Linux VM with the Azure portal
- Azure Disk Encryption Extension Schema for Linux
- Creating and configuring a key vault for Azure Disk Encryption
- Azure Disk Encryption sample scripts
- Azure Disk Encryption troubleshooting
- Azure Disk Encryption frequently asked questions
Azure disk encryption with Azure AD (previous version)
- Overview of Azure Disk Encryption with Azure AD for Linux virtual machines
- Azure Disk Encryption with Azure AD scenarios on Linux VMs
- Creating and configuring a key vault for Azure Disk Encryption with Azure AD (previous release)
Windows virtual machines
The following articles provide guidance for encrypting Windows virtual machines.
Current version of Azure Disk Encryption
- Overview of Azure Disk Encryption for Windows virtual machines
- Azure Disk Encryption scenarios on Windows VMs
- Create and encrypt a Windows VM with Azure CLI
- Create and encrypt a Windows VM with Azure PowerShell
- Create and encrypt a Windows VM with the Azure portal
- Azure Disk Encryption Extension Schema for Windows
- Creating and configuring a key vault for Azure Disk Encryption
- Azure Disk Encryption sample scripts
- Azure Disk Encryption troubleshooting
- Azure Disk Encryption frequently asked questions
Azure disk encryption with Azure AD (previous version)
- Overview of Azure Disk Encryption with Azure AD for Windows virtual machines
- Azure Disk Encryption with Azure AD scenarios on Windows VMs
- Creating and configuring a key vault for Azure Disk Encryption with Azure AD (previous release)
Virtual machine scale sets
The following articles provide guidance for encrypting virtual machine scale sets.
WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues
This page exists only to help migrate existing data encrypted by TrueCrypt.
The development of TrueCrypt was ended in 5/2014 after Microsoft terminated support of Windows XP. Windows 8/7/Vista and later offer integrated support for encrypted disks and virtual disk images. Such integrated support is also available on other platforms (click here for more information). You should migrate any data encrypted by TrueCrypt to encrypted disks or virtual disk images supported on your platform.
Migrating from TrueCrypt to BitLocker:
If you have the system drive encrypted by TrueCrypt:
- Decrypt the system drive (open System menu in TrueCrypt and select Permanently Decrypt System Drive ). If you want to encrypt the drive by BitLocker before decryption, disable Trusted Platform Module first and do not decrypt the drive now.
Encrypt the system drive by BitLocker. Open the Explorer:
Click the drive C: (or any other drive where system encryption is or was used) using the right mouse button and select Turn on BitLocker :
If you do not see the Turn on BitLocker menu item, click here.
Alternatively, use search in the Start menu or screen:
If you do not see the BitLocker item, click here.
If BitLocker reports Trusted Platform Module (TPM) unavailable error, click here.
If you have a non-system drive encrypted by TrueCrypt:
- If you have a spare or backup drive (having sufficient space to store all data you need to migrate to BitLocker), encrypt it by BitLocker (click the drive in Explorer using the right mouse button and select Turn on BitLocker ):
If you do not see the Turn on BitLocker menu item, click here.
Copy all data from the drive encrypted by TrueCrypt to the drive encrypted by BitLocker.
If you do not have a spare drive, first decrypt the drive encrypted by TrueCrypt. Select the drive in TrueCrypt, open the Volumes menu and select Permanently Decrypt item (available in version 7.2). Then encrypt the drive by BitLocker (see above).
To mount a drive encrypted by BitLocker, open the drive in Explorer.
To dismount a removable drive encrypted by BitLocker, use Eject menu item or Safely Remove icon:
To dismount a non-removable drive encrypted by BitLocker, use Offline item in the context menu of the drive in Disk Management window:
To mount the drive again, use Online item in the context menu of the drive.
If you have a file container encrypted by TrueCrypt:
- Create a new virtual disk file (VHD). Open the Computer Management window (click the Computer or PC icon using the right mouse button and select Manage ):
Select the Disk Management item:
Alternatively, use search in the Start menu or screen:
Open Action menu in the Disk Management window and select Create VHD :
Create and attach a new virtual disk file (VHD):
Initialize the new virtual drive. Click the new disk icon using the right mouse button and select Initialize Disk :
Create a partition on the virtual drive. Click the unallocated space using the right mouse button and select New Simple Volume :
Encrypt the new virtual drive by BitLocker. Click the drive in Explorer using the right mouse button and select Turn on BitLocker :
If you do not see the Turn on BitLocker menu item, click here.
Copy all data from the mounted TrueCrypt file container to the new virtual drive encrypted by BitLocker.
To dismount the drive, click the drive using the right mouse button in Explorer and select Eject :
To mount the drive again, double click the virtual disk file (requires Windows 8 or later):
Alternatively, use Attach VHD in the Action menu of the Disk Management window:
Download:
WARNING: Using TrueCrypt is not secure
You should download TrueCrypt only if you are migrating data encrypted by TrueCrypt.
If you use TrueCrypt on other platform than Windows, click here.
In case of theft of your computer, there is a thread that your data will get stolen as well. If your hard drive is not secured properly, it is easier than you might think to steal your data. Owners of Apple devices are in a much easier situation as Apple has encrypted all their computers and laptops by default, therefore, all the stored data is safe. Data stored on devices with Windows and some versions of Linux need to be protected by their owners themselves.
To protect your data, Windows (or Linux) login and password is not enough. This is just to prevent your children or colleagues at work from having access to your data. This protects your data from the user perspective. An experienced thief though who is after your data, can overcome this kind of protection very easily. How? By simply removing a few screws from your computer, taking out your Hard Drive and connecting it to some other computer. This instantly gives him access to all your data stored on the drive.
So how can you prevent data on your computer from being read so easily? How to better protect it? You have basically two options:
Locking your hard drive with password (HDD password) is the easiest option. To do so, no specialized software is needed. The lock just has to be turned on on your device.This kind of protection is weaker than encryption, but still better than none. It can be useful when a computer or notebook is lost or stolen, as it protects the data on the drive itself so nobody can access it by simply removing the HDD and connecting it to some other computer. The access to data is controlled by the drive itself and is only granted after entering the password even before the operating system starts when turning on your device. This means that you will have to enter the password on the “black screen”, the initial startup screen, that shows what key to press to get to the setup (most often F10, F2, Esc, Del) where the HDD password can be entered. The advantage is that the lock is directly on the hard drive and, unlike Windows password, is not dependent on the operating system of the computer or laptop.
Full disk encryption is the only truly safe option. If your disk is encrypted, the thief will not be able to get access to any of your data. If you are a user of an Apple device, encryption is turned on by the manufacturer and you don’t have to worry about anything. On the other hand, Windows, Android and (some versions of) Linux users have to turn on the disk encryption by themselves. As to Windows, devices from Windows Pro on (Windows Home doesn’t have this option) have the ability to enable a built-in disk encryption called Bitlocker. Likewise, Android and Linux have the ability to turn on such encryption. You can also use specialized disk encryption software.
So what hard disk protection should I choose?
Every kind of protection is better than none. This is particularly true for disks (or other data media) used for storing or transmitting data that should never get into unauthorized hands. So what are the hard disk security options? The best protection is without doubt encryption. Imagine the disk as a cabinet in which you store information:
- An unsecured disk is like a lockless cabinet – anyone who can access the room where the cabinet is placed can simply open the door and access all the information stored in the cabinet
- A password-locked disk is like a locked cabinet – information stored in there are secured in some way, but all you need to steal the information is to somehow overcome the lock
- An encrypted disk is like a locked cabinet where all the information is stored in a secret language that only you can understand (or anyone who has the key to decipher). In this case, even if the thief overcomes the security lock, he won’t be able to read any of your data.
What disk encryption tools are there?
There are quite a few pieces of software for disk encryption on the market. Some systems already contain such a tool. Here are some examples of dedicated encryption software:
- Bitlocker (Windows component)
- Veracrypt
- AxCrypt
- Symantec Endpoint Encryption
- DiskCryptor
Related terms and methods:
- Confidential Information
- Data Storage Device
- Encryption
- Flash Memory
- Hard Drive
- Hard Drive Password
- HDD (Hard Disk Drive)
- Sensitive information
- SSD (Solid State Disk)
- USB disk
Today, let’s take a look on encrypting your drive on Ubuntu 18.04. Note that all the Ubuntu flavors and Ubuntu-based distros will support the guides. No need to worry about compatibility.
Encrypting a drive has both its benefits and disadvantages. Let’s talk about them first.
The benefits are numerous.
- Increased privacy protection.
- No one can break the data, not with current technology. Even cracking a single file may take 1000+ years.
There are some disadvantages as well.
- If you forget the key, the data is as good as lost.
- Data recovery is impossible.
- The partition won’t be accessible to other systems and may cause SERIOUS compatibility issues.
For the protection of the data, you must remember the pass phrase, no matter what.
Encrypting machine’s host drive
Well, let’s jump into the encryption part. Whenever you install Ubuntu, you can have an encrypted drive right away. If you don’t remember how to install Ubuntu, let’s check out installation procedure of Ubuntu 18.04.
Thanks to the power of VirtualBox, we’re right into the installation of Ubuntu 18.04!
As soon as you arrive at this stage, check the option to encrypt the new Ubuntu installation for security. Choosing the LVM option is optional but good if you go with that.
At the next step, you’ll have to choose the security key that you’ll have to enter each time your computer boots up.
Continue the installation normally. Note that you will have to configure another password for logging into your user account.
Complete the installation as usual and restart the system.
Once the system starts, you will have to enter the passkey for the encrypted drive. Without the pass key, system won’t boot either. There’s literally no way to bypass it, literally NO WAY!
Encrypting a USB flash drive
Do you have a personal USB flash drive? Want to encrypt it? Let’s do it!
At first, we need a tool – GNOME Disk Utility. Run the following commands to install it –
Start the disk utility tool. It should be present with the name – Disks.
Now, connect the USB flash drive.
Unmount the drive’s partition.
After unmounting, time to format the drive. That’s why make sure that the drive doesn’t contain any important data beforehand.
Select to format with “Ext4” file system and LUKS enabled. You can choose to erase but it will take longer time depending on the size of the drive/partition.
Create a password for the new encrypted partition.
Confirm every details and format the drive. Wait until the process finishes.
Now, you can see that the drive has a protected partition. You can easily lock it down with one click.
Each time you access the drive, you’ll have to enter the passphrase.
Similarly, you can perform the lock any partition present in your system. Make sure to back up all the important data present as the formatting step will make them unavailable.
Voila! Happy encryption!
About the author
Sidratul Muntaha
Student of CSE. I love Linux and playing with tech and gadgets. I use both Ubuntu and Linux Mint.
Data protection with encryption for desktops, laptops, and removable media
Overview
The proliferation of data and devices in today’s enterprises has increased the complexity of protecting confidential data, meeting compliance mandates, and preventing costly data breaches. These challenges are further amplified as more and more employees bring their own computing devices to work. Ensuring that sensitive data is secured in the case of device loss has never been more difficult.
Trend Micro™ Endpoint Encryption encrypts data on a wide range of devices, such as PCs and Macs, laptops and desktops, USB drives, and other removable media. Available as a separate agent, this solution combines enterprise-wide full disk, file/folder, and removable media encryption to prevent unauthorised access and use of private information. A single, well-integrated management console allows you to manage your users holistically—using the same console for endpoint protection and other Trend Micro security products. Deploying the Endpoint Encryption agent helps ensure that your data will continue to be protected as your mobile computing devices and organisational needs change.
Download
Datasheet
Software and Hardware
- Laptops, desktops
- Removable media: USB/CD/DVD
- Files and file volumes (folders)
- Privacy
- Data protection
- Regulatory compliance
- Securing intellectual property
Maximise Platform Coverage for Data and Device Encryption
Get comprehensive data protection on Macs and PC laptops, desktops, removable media, and mobile devices
- Encrypt private data with fully integrated full disk, file folder, USB, and removable media encryption
- Support and leverage flexible hardware and software-based encryption across mixed environments
- Support self-encrypting TCG OPAL and OPAL 2 SED drives from Seagate, SanDisk ® , and Intel ®
- Simplify deployment and management with support for unified extensible firmware interface (UEFI), multiple physical drives, and pre-boot screen customisation
- Enable automatic and transparent encryption without performance degradation
Lower Total Cost of Ownership (TCO) with Centralised Policy Administration and Transparent Key Management
Save more with an integrated solution that makes it easy to deploy, configure, and manage encryption
- Manage the encryption policy alongside all endpoint security policies with integration to a common management console, Trend Micro™ Control Manager™
- Gain visibility and control over encryption, monitoring, and protection of data
- Automate policy enforcement with remediation of security events, without the burden of encryption key management
- Tight integration with Trend Micro™ Integrated Data Loss Prevention (iDLP) delivers content-based encryption for data at rest and in motion
Simplify Remote Device Management
- Maintain compliance and protect your data without disrupting users in the event of a lost device or forgotten password
- Manage policies and protect data on PCs, Macs, laptops, desktops, USBs, and removable media
- Collect device-specific information such as device attributes, directory listing, and unique device IDs based on device name, MAC address, and central processing unit (CPU) identifier
- Improve protection for remote devices with tools to remotely lock, reset, or “kill” lost or stolen devices—even before a device boots using network-aware pre-boot authentication
Advanced Reporting and Auditing
- Unify visibility and policy deployment with other Trend Micro products through integration with Control Manager
- Automate enforcement of regulatory compliance with policy-based encryption
- Receive detailed auditing and reporting by individual, organisational unit, and device
- Assist compliance initiatives with an audit trail for all administrative actions
- Demonstrate compliance on demand with real-time auditing
Administrative Tools and Active Directory Integration
- Provide remote one-time passwords across all endpoint client applications
- Manage users and groups from multiple active directory domains in a single console, simplifying the existing IT infrastructure for deployment and management
- Gain access to recovery console in the Microsoft ® Windows ® pre-boot
- Gain flexible authentication, including active directory integration, fixed password, and multi-factor authentication for government and defence customers
- Ensure that lost or stolen devices can be remotely wiped or locked before they can boot using network-aware (WiFi and ethernet)
- Enable policy updates prior to authentication
- Trigger the lockout feature in response to incorrect authentication attempts
- Configure actions on failed password attempt threshold
- Support multiple user and administrator accounts per device
Support for a Consumerised Environment
- Provide management and visibility for Microsoft ® BitLocker ® , this is especially useful for employee-owned devices where corporate data needs to be protected.
- Provide visibility and management of Apple ® FileVault ® to enforce policies on Macs, and protect them in the case of loss or theft.
Data Encryption Solutions
Encryption offers protection by scrambling data, so only the owner of the key or password can read the data.
Two types of encryption are available to members of the UVA community: hard drive/file encryption and Virtual Private Network (VPN) software.
Hard Drive and/or File Encryption:
When you have no option other than to store highly sensitive data on your individual-use computer or media, and such storage has been approved, you must encrypt your hard drive or the relevant files on your computer’s drive. If you lose your computer or electronic media, the encryption will protect the data and render it invisible to anyone but you, since you alone know the password.
Anyone can encrypt their hard drive regardless of the classification of the stored data. Both Mac and Windows offer native full disk encryption. Consider LUKS for Linux. For guidance, please check with your LSP and with us by emailing [email protected] . Health Information and Technology (HIT) users should use encryption methods the HIT Security Office recommends.
Contact [email protected] with any questions.
The Virtual Private Network (VPN):
A VPN creates a private network over a public network as if you were directly connected to the private network. It also encrypts (scrambles) data as it is transmitted between your computing device and a server. This allows you to access sensitive data securely stored on a remote server. It’s always more secure to leave sensitive data on a server, where it is managed by a system administrator, and use a VPN to access it.
Both ITS and HIT offer a VPN solution for members of the UVA community.
Before installing: You will have to download and install a personal digital certificate, and possibly, download and install a VPN client. See
If you need help: Contact your Local Support Partner (LSP), the UVa Help Desk, or the HIT Help Desk at 434-924-5334.
Whole Disk Encryption (WDE)
You remember sitting your laptop right there. You only turned your back for a second! Now the computer has disappeared and the data on it is at risk. Physical security will always present a challenge to information security. It is important the university’s data be protected when these mishaps occur.
Protecting the university from data breach as a result of lost or stolen devices.
The loss or theft of unencrypted endpoint computers that contain sensitive data results in a high risk of the data being compromised, leading to an expensive breach notification. Whole Disk Encryption (WDE) solutions prevent the unauthorized disclosure of data on endpoint computers in the event the device is lost or stolen. It works by encrypting a system’s entire hard drive including the operating system and all applications and data stored on it.
The use of whole disk encryption allows the university to ensure that sensitive data residing on endpoint computers is protected against unauthorized access. In the event that an encrypted computer is lost or stolen, the risk of unauthorized access to that data is greatly reduced. This provides the university with substantial cost savings over time, as well as helping to improve its reputation for protecting its constituents’ personal data.
Expand all What is whole disk encryption?
Whole disk encryption is a technology which protects information by converting it into unreadable code that cannot be deciphered easily by unauthorized people.
Whole disk encryption works by encrypting a system’s entire hard drive including the operating system and all applications and data stored on it. Authorized users will have and maintain a key (password) that allows access to files and data.
South Carolina state policy requires whole disk encryption on computers that store sensitive data. To protect user privacy and non-sensitive university data, the solution is recommended for all others.
Contact your local security liaison, system administrator, or SA contact if you believe you require whole disk encryption of your computer. Installation priority will be given to those devices that store sensitive data.
Solution
SecureDoc by WinMagic
The SecureDoc by Winmagic Whole Disk Encryption (WDE) solution allows system administrators to protect sensitive data on university-owned Windows, Mac, and Linux endpoint computers and USB drives.
At this time, DoIT is only supporting Windows applications.
- Documents
- User Manual [pdf]
Quick Links
- WinMagic
- Documentation (login required)
- MY.SC.EDU (login required)
- Securing the Human Awareness Training (login required)
Premium protection for classified
and sensitive data
Providing hardware encrypted solid state drive (SSD) and hard disk drive (HDD) solutions for any platform or application
Millions of computers are lost or stolen every year. Protecting the classified and sensitive data at risk of breach is more important than ever. Viasat Eclypt ® accredited, encrypted solid state drives and hard drives, using hardware encryption for the highest level of security, provide premium endpoint protection for data at rest (DAR) at multiple classification levels for End User Devices (EUDs) and air, land and sea platforms.
- Internal, external, portable, solid-state drive (SSD), and ruggedized hard drive configurations
- Custom-made systems and solutions
Eclypt® technology
The Viasat Eclypt range is a family of encrypted drives that protects data at rest in servers and desktop computers in enterprise and tactical environments, as well as data stored in vehicles, aircraft, UAVs or on person. Viasat’s Eclypt technology combines sophisticated authentication, full disk encryption and data storage into tamper-evident hardware for safeguarding your data and is accredited by organisations around the world, including NCSC, to protect important data. 256-bit AES Hardware encrypted storage provides the best security solution for your data.
Eclypt® products
The products within the Eclypt range are tailored for each generic use case and cover such a wide range of enterprise and tactical environment encryption and authentication scenarios, creating the perfect solution for your data at rest requirements.
Over the last 10 years of Eclypt, Viasat UK has worked together with clients to customise and develop bespoke Eclypt solutions for unique situations and extreme conditions.
The Eclypt® Core 256-bit hardware encrypted internal SSD and HDD protects data at rest in COTS laptop and desktop computers. During high-risk operations, this full disk encryption solution protects your valuable data on both manned and unmanned mobile platforms with accredited hardware-based security.
The Eclypt ® Freedom is an external portable USB3.0 256-bit hardware encrypted SSD and HDD that can store, archive, or back up data at rest and easily transport it to different computers.
The Eclypt® secure data recorder (SDR) provides multi-channel secure data recording for manned and unmanned platforms operating in air, land, and sea environments. The SDR helps ensure that data is safely stored throughout mission operations as well as during the transfer of data on and off all types of platforms.
- Eclypt® Core
- Eclypt® Freedom
- Eclypt® Secure Data Recorder
The Eclypt® Core encrypted internal hard drive protects data at rest in COTS laptop and desktop computers and is certified for the United Kingdom (U.K.), the North Atlantic Treaty Organization (NATO), and more. During high-risk operations, this self-encrypting hard drive protects your valuable data on both manned and unmanned mobile platforms with accredited hardware-based security. In the event of computer theft, loss, or attack, the hard drive helps ensure that your data is completely protected and secure.
- Provides accredited protection: U.K. Top Secret and below, Canada Top Secret and below, NATO Secret and below, and Federal Information Processing Standards (FIPS) 140-2 (historic)
- 2.5″ x 7mm SSD
- 3.5″ x 25.4mm HDD and SSD
- Works independently of any operating system, application, service pack or software patch
- Uses remote authentication to encrypt data in remote or hard-to-access locations
- Offers a unique tamper-proof and tamper-evident construction
- Offers multiple user profiles in a 3-tier management system
- Provides lifetime key (user-defined with protection level 200)
- Non-volatile keys are stored within tamper-proof device, protected by AES-256 keywrap
- Windows ® /Linux based software* provides easy-to-use management and authentication functionality
The Eclypt ® Freedom is an external USB hardware-encrypted hard drive that can store, archive, or back up data at rest and easily transport it to different computers.
Used by governments, military forces, and law enforcement organizations worldwide, this secure portable hard drive integrates sophisticated authentication, entire-disk encryption, and data storage into tamper-resistant portable hardware that safeguards your data.
- Provides accredited protection: U.K. Top Secret and below, Canada Top Secret and below, NATO secret and below
- Offers USB connectivity for seamless portability
- Provides unique tamper-proof and tamper-evident construction
- Offers multiple user profiles in a 3-tier management system
- Provides lifetime key
- Non-volatile keys are stored within tamper-proof device, protected by AES-256 key wrap
Co-developed by Viasat and General Dynamics U.K., the Eclypt® secure data recorder (SDR) provides multi-channel secure data recording for manned and unmanned platforms operating in air, land, and sea environments. The SDR helps ensure that data is safely stored throughout mission operations as well as during the transfer of data on and off all types of platforms.
The SDR is based on the certified Viasat Eclypt ® 600 encrypted hard drive and has been adapted for harsh operating environments. This technology is field-proven on the U.K. Future Lynx Wildcat helicopter program and provides a low-risk approach to applying existing certified Viasat encryption and flexible data interfaces for large storage capacity (512 GB+) requirements.
There are three SDR models:
- SDR-100 data-only recorder: stores large amounts of mission data
- SDR-200 standard-definition video recorder: records up to eight channels of standard-definition video; ideal for retrofit applications
- SDR-300 high-definition video recorder: records up to four channels of high-definition video
Published on March 20, 2018
Introduction
DigitalOcean Volumes are scalable, SSD-based block storage devices. Volumes allow you to create and expand your infrastructure’s storage capacity without needing to resize your Droplets.
Volumes are encrypted at rest, which means that the data on a Volume is not readable outside of its storage cluster. When you attach a Volume to a Droplet, the Droplet is presented with a decrypted block storage device and all data is transmitted over isolated networks.
For additional security, you can also create a file system in a LUKS encrypted disk on your Volume. This means that the disk will need to be decrypted by the operating system on your Droplet in order to read any data.
This tutorial covers how to:
- Create a passphrase-protected encrypted disk on your Volume containing a file system.
- Manually mount the encrypted file system for use, then unmount and relock it when you’re done.
- Automatically mount the file system when the Droplet boots.
Prerequisites
To follow this tutorial, you will need:
Warning: This process is destructive to any data on the Volume. Be sure to either start with a new Volume or back up your data before reformatting an existing Volume.
Step 1 — Creating the Encrypted Disk
cryptsetup is a utility used to manage LUKS volumes in addition to other encrypted formats. To begin, use cryptsetup to initialize an encrypted disk on your Volume.
Make sure to replace volume-lon1-01 with the name of your Volume. The -y flag will require you to enter your passphrase twice when you’re prompted to create it. The -v flag adds additional human-readable output to verify the success of the command.
The output will ask you to confirm overwriting the data on the Volume. Type YES in all caps, then press ENTER to continue.
Next, the output will prompt you to create a passphrase for the encrypted disk. Enter a unique, strong passphrase and verify it by entering it a second time. This passphrase is not recoverable, so keep it recorded in a safe place.
If you need to, you can change this passphrase in the future with the cryptsetup luksChangeKey command. You can also add up to 8 additional passphrases per device with cryptsetup luksAddKey .
At this point, your disk is created and encrypted. Next, decrypt it and map it to a label for easier referencing. Here, we’re labeling it secure-volume , but you can label it with anything you like.
You’ll be prompted for the passphrase. Once you enter it, the Volume will now be mapped to /dev/mapper/secure-volume .
To make sure everything worked, verify the details of the encrypted disk.
You’ll see output like this indicating the Volume label and type.
At this point, you have a passphrase-protected encrypted disk. The next step is to create a file system on that disk so the operating system can use it to store files.
Step 2 — Creating and Mounting the File System
Let’s first take a look at the current available disk space on the Droplet.
You’ll see output similar to this, depending on your Droplet configuration:
Right now, /dev/mapper/ secure-volume doesn’t show up on this list because the Volume isn’t yet accessible to the Droplet. To make it accessible, we need to create and mount the file system.
Use the mkfs.xfs utility (make file system) to create an XFS file system on the volume.
Once the file system is created, you can mount it, which means making it available to the operating system on your Droplet.
Create a mount point, which is where the file system will be attached. A good recommendation for a mount point is an empty directory in the /mnt directory, so we’ll use /mnt/ secure .
Then mount the file system.
To make sure it worked, check the available disk space on your Droplet again.
You’ll now see /dev/mapper/ secure-volume listed.
This means your encrypted file system is attached and available for use.
When you no longer need to access the data on the Volume, you can unmount the file system and lock the encrypted disk.
You can verify with df -h that the file system is no longer available. In order to make the data on the Volume accessible again, you would run through the steps to open the disk ( cryptsetup luksOpen . ), create a mount point, and mount the file system.
To avoid going through this manual process every time you want use the Volume, you can instead configure the file system to mount automatically when your Droplet boots.
Step 3 — Automatically Mounting the File System on Boot
The encrypted disk can have up to 8 passphrases. In this final step, we’ll create a key and add it as a passphrase, then use that key to configure the Volume to be decrypted and mounted as the Droplet is booting.
Create a key file at /root/.secure_key . This command will make a 4 KB file with random contents:
Adjust the permissions of this key file so it’s only readable by the root user.
Then add the key as a passphrase for the encrypted disk.
You’ll be prompted for a passphrase. You can enter the one you set when you first created the encrypted disk.
/etc/crypttab is a configuration file that defines encrypted disks to set up when the system starts. Open this file with nano or your favorite text editor.
Add the following line to the bottom of the file to map the Volume at boot.
The format of the lines in /etc/crypttab is device_name device_path key_path options . Here, the device name is secure-volume (or the name you chose instead), the path is /dev/disk/by-id/ . , the key file is what we just created at /root/.secure_key , and the options specify luks encryption.
Save and close the file.
/etc/fstab is a configuration file to automate mounting. Open this file for editing.
Add the following line to the bottom of the file to automatically mount the disk at boot.
The first three arguments of the lines in /etc/fstab are always device_path mount_point file_system_type . Here, we have the same device path and mount point as in Step 2, and we specify the XFS file system. You can read about the other fields in fstab ’s man page ( man fstab ).
Save and close the file. Your encrypted file system is now set to automatically mount when your Droplet boots. You can test this by rebooting your Droplet, but be cautious with any running services.
Conclusion
By default, DigitalOcean Volumes are encrypted when they are not attached to a Droplet. In this tutorial, you added an additional layer of security by putting a file system in an encrypted disk on a Volume. You can create an encrypted disk, add passphrases to it, and mount it manually or automatically for use within the Droplet.
You can learn more about DigitalOcean Block Storage Volumes in the Getting Started with DigitalOcean Block Storage series.