How to use android’s wi-fi assistant to safely connect to public wi-fi networks (and save data)

Joseph Russell
Published Mar 29, 2026
Cameron Summerson is the Editor in Chief of Review Geek and serves as an Editorial Advisor for How-To Geek and LifeSavvy. He’s been covering technology for nearly a decade and has written over 4,000 articles and hundreds of product reviews in that time. He’s been published in print magazines and quoted as a smartphone expert in the New York Times. Read more.
Google recently introduced a new feature into Android 8.1 Oreo that displays how good a public Wi-Fi network is before you connect to it. Using just simple terms like Slow, OK, Fast, and Very Fast, it will let you quickly gauge whether a network is worth connecting to, or if you’re better off just sticking with mobile data.
How Does Google Know the Quality of a Network?
Android is relying on the Usage & Diagnostics sharing feature to crowdsource this data. When you connect your phone to an open network, say at Starbucks for example, the speed of this network (along with other information) is shared with Google. On a long enough timeline, as people continue to connect to the network and the information is shared with Google, a baseline for speed and reliability is established.
Once that baseline is clear, the Network Ratings feature is able to reliably tell you how good a network is before you connect to it…as long as its popular enough. Your local mom and pop coffee shop might not get a rating, or may take longer, if it’s less trafficked than the local Starbucks.
So, Google Is Collecting Data From Me? I Don’t Like That!
In a world where personal information being shared is a constant concern for many, you’d be remiss to not at least wonder how secure this feature is—especially on the sharing end. The short answer here is that the data is, like most shared data, anonymous. Google isn’t collecting what you’re doing while connected to these public networks—though we should definitely mention you shouldn’t be doing anything personal while on a public network anyway—just the most basic of data.
Of course, the Usage & Diagnostics feature used to collect the network data is about more than just network data. This is a very generalized data collection tool, which helps Google “improve products and services for everyone.” This includes your battery level, how often apps are opened, and the quality/length of network connections for both Wi-Fi and Bluetooth.
Google also details how it uses this information on the Usage & Diagnostics support page, but here’s the pertinent bit:
Google uses usage and diagnostics information to improve products and services, like Google apps and Android devices. All information is used in accordance with Google’s Privacy Policy.
For example, Google can use usage and diagnostics information to improve:
- Battery life
Google can use information about what’s using the most battery on your device to help make common features use less battery. - Crashing or freezing on devices
Google can use information about when apps crash and freeze on your device to help make the Android operating system more reliable.
Some aggregated information can help partners, like Android developers, make their apps and products better, too.
If you’re not on board with sending this sort of into back to Google, thankfully it’s optional.
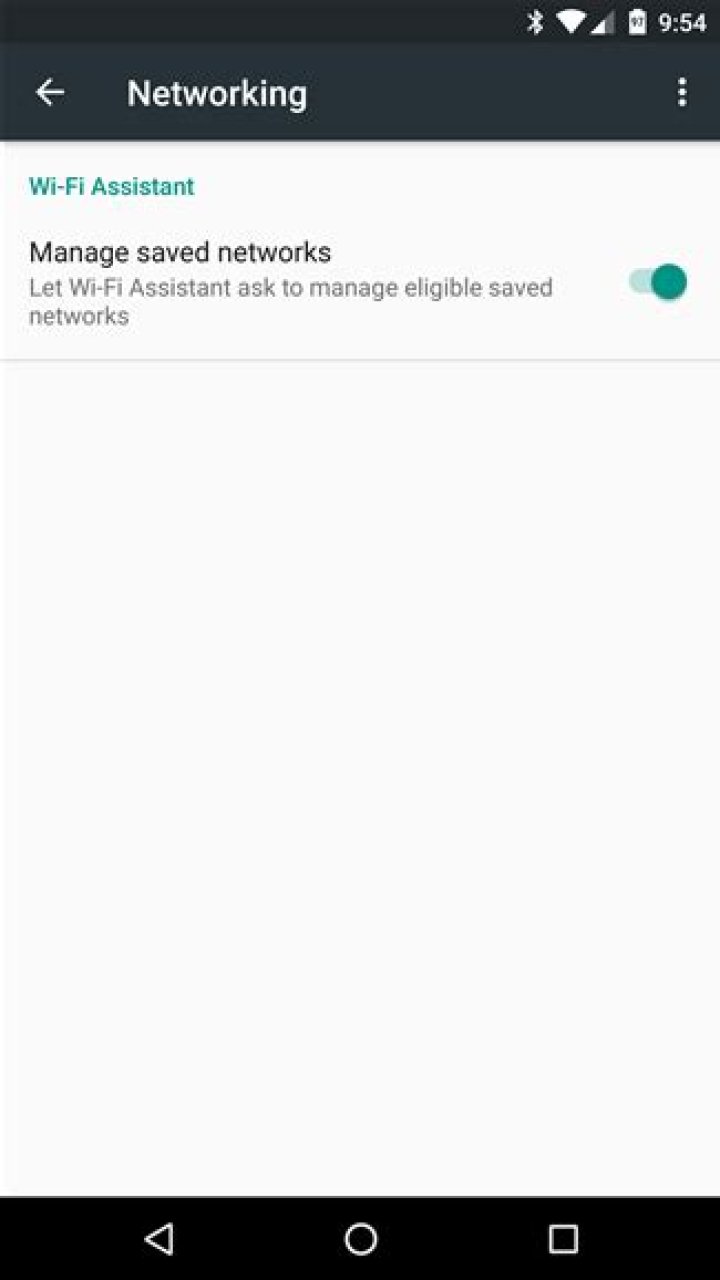
How to Disable Usage & Diagnostics Sharing
To disable Usage & Diagnostics Sharing, open your phone’s Settings menu by pulling the notification shade and tapping the cog icon.
From there, scroll down to Google and tap on it.
Tap the three dots in the upper right corner, then choose “Usage & Diagnostics”
Slide the toggle off here, and you’re out. No more information will be shared from your phone, though you’ll still see all the benefits of the info that shared from other users—like Network Ratings.
You can create a profile with specific WiFi settings, and then deploy this profile to your Android devices. Microsoft Intune offers many features, including authenticating to your network, adding a PKCS or SCEP certificate, and more.
This feature applies to:
- Android device administrator (DA)
These Wi-Fi settings are separated in to two categories: Basic settings and Enterprise-level settings. This article describes these settings.
Before you begin
Basic
- Wi-Fi type: Choose Basic.
- SSID: Enter the service set identifier, which is the real name of the wireless network that devices connect to. However, users only see the network name you configured when they choose the connection.
- Hidden network: Choose Enable to hide this network from the list of available networks on the device. The SSID isn’t broadcasted. Choose Disable to show this network in the list of available networks on the device.
Enterprise
Wi-Fi type: Choose Enterprise.
SSID: Enter the service set identifier, which is the real name of the wireless network that devices connect to. However, users only see the network name you configured when they choose the connection.
Hidden network: Choose Enable to hide this network from the list of available networks on the device. The SSID isn’t broadcasted. Choose Disable to show this network in the list of available networks on the device.
EAP type: Choose the Extensible Authentication Protocol (EAP) type used to authenticate secured wireless connections. Your options:
EAP-TLS: Also enter:
Server Trust – Root certificate for server validation: Choose an existing trusted root certificate profile. This certificate is presented to the server when the client connects to the network. It authenticates the connection.
Client Authentication – Client certificate for client authentication (Identity certificate): Choose the SCEP or PKCS client certificate profile that is also deployed to the device. This certificate is the identity presented by the device to the server to authenticate the connection.
Identity privacy (outer identity): Enter the text sent in the response to an EAP identity request. This text can be any value, such as anonymous . During authentication, this anonymous identity is initially sent, and then followed by the real identification sent in a secure tunnel.​
EAP-TTLS: Also enter:
Server Trust – Root certificate for server validation: Choose an existing trusted root certificate profile. This certificate is presented to the server when the client connects to the network. It authenticates the connection.
Client Authentication: Choose an Authentication method. Your options:
Username and Password: Prompt the user for a user name and password to authenticate the connection. Also enter:
Non-EAP method (inner identity): Choose how you authenticate the connection. Be sure you choose the same protocol that’s configured on your Wi-Fi network. Your options:
- Unencrypted password (PAP)
- Challenge Handshake Authentication Protocol (CHAP)
- Microsoft CHAP (MS-CHAP)
- Microsoft CHAP Version 2 (MS-CHAP v2)
Certificates: Choose the SCEP or PKCS client certificate profile that is also deployed to the device. This certificate is the identity presented by the device to the server to authenticate the connection.
Identity privacy (outer identity): Enter the text sent in the response to an EAP identity request. This text can be any value, such as anonymous . During authentication, this anonymous identity is initially sent, and then followed by the real identification sent in a secure tunnel.
PEAP: Also enter:
Server Trust – Root certificate for server validation: Choose an existing trusted root certificate profile. This certificate is presented to the server when the client connects to the network. It authenticates the connection.
Client Authentication: Choose an Authentication method. Your options:
Username and Password: Prompt the user for a user name and password to authenticate the connection. Also enter:
Non-EAP method for authentication (inner identity): Choose how you authenticate the connection. Be sure you choose the same protocol that’s configured on your Wi-Fi network. Your options:
- None
- Microsoft CHAP Version 2 (MS-CHAP v2)
Certificates: Choose the SCEP or PKCS client certificate profile that is also deployed to the device. This certificate is the identity presented by the device to the server to authenticate the connection.
Identity privacy (outer identity): Enter the text sent in the response to an EAP identity request. This text can be any value, such as anonymous . During authentication, this anonymous identity is initially sent, and then followed by the real identification sent in a secure tunnel.
Next steps
The profile is created, but it’s not doing anything. Next, assign this profile.
More resources
Using Android Enterprise or Android Kiosk devices? If yes, then look at Wi-Fi settings for devices running Android Enterprise and dedicated devices.
Public Wi-Fi is one of those catch-22 scenarios of the modern world. On the one end, it allows you to access the Internet for free. But, on the other hand, it makes you vulnerable to cybercrime and hacking and puts your online privacy in danger.
The problem is that Wi-Fi networks are not protected by encryption technology. This means anyone from within the network can easily access your Internet data. That goes for all the usernames, passwords, credit card information and chat messages that you send and receive while connected to the Wi-Fi network.
However, there are ways to stay safe on public Wi-Fi networks and we’re going to show you how.
Why is Your Privacy at Risk on Public Wi-Fi?
Online hackers are constantly working to improve the methods they use to steal data from Internet users. One of their most creative methods is man-in-the-middle (MITM). This involves creating their own fake public network which has the same details as the restaurant or café that you’re accessing the Wi-Fi network from. Once you log into the fake network, the hackers will be able to access all of your private information. This is regardless of the device you’re using.
Another common method is that of installing packet sniffing software. This enables them to record all the data from users who’re online on that particular network.
This is just the tip of the iceberg when it comes to techniques that hackers can and do use to infiltrate user data on Wi-Fi networks. The worst part is that most of these methods are freely available online for anyone to use. So you never know who’s a hacker and who isn’t.
Attention: Read before you continue
Governments and ISPs across the world monitor their users online activities. If found streaming or browsing content on your Fire TV Stick, mobile or PC, you could get into serious trouble.
Currently, the following information is visible:
- Your IP:
- Your Country:
- Your City:
- Your ISP:
If this is your real information, you need to use a VPN to protect your identity.
We strongly recommend you to get a good VPN and hide your identity so that your online experience doesn’t take a bad turn.
We use IPVanish which is the fastest and most secure VPN in the industry. It is very easy to install on any device including Amazon Fire TV Stick. Also, it comes with a 30-day money-back guarantee. If you don’t like their service, you can always ask for a refund. IPVanish also runs a limited time offer where you can save 74% on your VPN and they allow you to use one account on unlimited devices.
This is a flash sale that can expire at any time!
Table of Contents
In this post, we are going to talk about using public Wi-Fi hotspots and doing it securely. So on public Wi-FI hotspots like the coffee shop, restaurant, etc, the owner of the Hotspot is a man in the middle so can both observe and inject into any traffic you send unencrypted. Other users on the network can try to observe your traffic, inject packets into your traffic to attack you, and attack you directly via open ports. The hotspot you connect to might not even be the real one you think you’re connecting to and be replaced by an evil twin so there are many known risks. So let’s go through some mitigations and see how many of these you would have come up with yourself
Mitigations
Avoidance
Avoid using public wi-fi hotspots if possible which reduces the risk to zero. If you can use Ethernet instead of Wi-Fi that is a preference for no fewer types of attack but generally we know that these things are not very convenient but the first step is to always avoid them if you can since wifi is vulnerable to packet sniffers.
Switch off when not in use
Switch off or disable all of your wireless technology unless you’re using it. It’s safer and they actually save your battery and this includes Wi-Fi also Bluetooth, 3G they don’t need to be on if you’re not using them and it’s safer if you can only connect to hotspots you have some level of trust in, again this may not always be possible. Try to use hotspots that follow the security standards laid out in the section on Wi-Fi security and make sure they’re using WPA2 and if they’re using WEP anybody could be on it. You should still learn how to remove adware from Macs or Windows platforms as well as other malware.
Use Encryption
Without fail as an absolute minimum always use at least SSL NTFS encryption even if you’re not sending sensitive data without end to end encryption packets can be injected to attack you, to attack your browser unless you have an outstanding excuse then use an encrypted tunnel for all your traffic everything that is sent from your operating system.
Normally this is done with a VPN because the VPN will tunnel all traffic from your operating system but if you know what you’re doing you could also use SSH, JonDonym, Tor, they’re all fine but remember if you don’t set it up so the whole operating system is sending traffic encrypted you could have things in the background like maybe checking email for example that isn’t going over the encrypted tunnel so do make sure everything from the operating system has an extra layer of encryption to protect you.VPNs are recommended as an encryption solution so we suggest that you check out our antivirus with VPN lineup.
Disable services on ports that aren’t needed
Disable or switch off services running on your local ports that aren’t needed. This is just a general step of hardening for any operating system and to also help block access to those services or maybe you don’t want to switch them off or you just want to block them. You can use a host based firewall with an implicit deny to all inbound traffic unless it’s for some reason required but generally because you are on a wi-fi hotspot it’s very unlikely that any inbound traffic is going to be required so maybe have a firewall profile when you are on public hotspots and on public networks.
Physical Isolation
And finally, if you can, use a physical form of isolation with a portable router/firewall. This means getting yourself a hardware router/firewall and connecting via an ethernet cable which is safer instead of connecting your laptop or device to the hotspot which can prevent man-in-the-middle attacks. This provides a layer of physical separation and you connect to this device instead so this device can be used to form an encrypted tunnel and as a firewall.
1. Is it safe to use public WiFi with VPN?
Despite being connected to the internet and using VPN services, there is a coverage gap between connecting to public WiFi networks and turning on your VPN network connection. However, in public, using a VPN secure network is still far safer than connecting to a public network without any additional digital protection. A VPN app service provides an additional layer of protection by making your data secure or encrypts data traveling to and from your device and connecting you to a private server.
2. Can you trust public Wi-Fi?
It depends, according to security experts. While encryption has made web browsing safer, it does not eliminate risk. Long have security experts recommended users avoid public Wi-Fi networks due to the risk of being hacked. The majority of sensitive data is now transmitted via encrypted channels.
3. Can you get hacked using public Wi-Fi?
You’ve probably heard about the perils of accessing unprotected public Wi-Fi networks, and you’re aware that hackers are snooping about. It is relatively straightforward to hack into a laptop or any android devices that are connected to an unprotected public Wi-Fi network. Hackers are capable of reading your emails, stealing your passwords, and even hijacking your website login credentials. Additionally, if you connect to a Wi-Fi network and transmit data via websites or mobile apps, another party may be able to view it. Finally, avoid using previously used passwords or reusing the same password across numerous accounts, as a single breach can jeopardize them all.
4. Why is public Wi-Fi not safe?
The most severe threat to access public Wi-Fi networks security is the hacker’s ability to place himself between you and the connecting point. Additionally, hackers can disseminate malware via an insecure free Wi-Fi secure connection. Allowing file sharing across the same network makes it very easy for a hacker to install malicious software on your computer. Is it essential to have sharing preferences enabled when connected to public Wi-Fi networks? Not at all! Therefore, turn off file sharing immediately after verifying the network. File sharing is typically quite simple to disable via the system preferences or control panel, depending on your operating system.
5. Is it safe to use Facebook on public Wi-Fi?
You may not be aware, but you are particularly vulnerable while using a public WI-FI networks connection to access Facebook. This has the potential to result in identity theft, personal information hack, or even credit fraud. In addition, by connecting to a public Wi-Fi networks that provides unlimited Internet access, any Facebook user leaves themselves highly vulnerable to hacker assaults.
Navigating through the web can seem like a minefield. It looks like new threats emerge daily, and people need to follow strict rules to keep themselves safe.
However, there are occasions when users engage in suspicious activities and disregard basic cybersecurity tips. Public Wi-Fi spots are one of the menaces that nearly everyone uses. However, what happens when you connect to an unsecured Wi-Fi spot?
Because COVID-19 initiated a revolution in the way people work, many enterprises feel comfortable moving online for longer than expected. However, the sudden shift to remote work left many employees struggling to supply the same security level at home.
Usually, people are not eager to protect their home networks. Instead, they keep the default router passwords and fail to use powerful anti-virus programs.
Sadly, connecting to unsecured networks can lead to grave consequences on the employee’s and the company’s part. Let’s see how unsecured connections can compromise security and privacy. Also, let’s look for ways to solve these issues in cost-effective ways.
Risks of Using Public Wi-Fi
The most important thing you should know about using public networks is that there is usually no encryption.What does this mean? Anyone with relatively basic technical skills can prepare an intrusive device, spying on people connected to public Wi-Fi spots.
Such hackers can monitor your activities. If you make bank transactions, the crook can see the credentials you type.
Thanks to unsecured networks, we have the infamous man-in-the-middle attacks (MitM). Hackers can use their devices and configure them to act as access points between you and the public network.
All of your data will go through the cybercriminals’ access point. You will be giving away all your passwords, usernames, and credit card information without even knowing it.
A hacker can also install malware on your computer or smartphone to delete or steal data stored on your local storage. All of this does sound scary, but there are several tricks you can use to boost your cybersecurity even when using public Wi-Fi spots.
Don’t Use Sharing Features
Windows 10 has done a great job streamlining various activities for an average user. When it detects a Wi-Fi, and you choose to connect to it, you will be prompted to select whether it is a public or private network you are connecting to. If you choose Private, you are automatically turning file sharing. File sharing enables hackers to steal sensitive data from your computer.
You can easily check your settings. Click on your active internet connection and choose “Properties.” Under “Network profile,” make sure that “Public” is turned on. Congratulations, you’ve just added your first security layer while on a public network.
Use Internet Security Suites
An Internet Security Suite is a software that offers more protection than a simple anti-virus solution. With one of the best suites active on your computer, you will be able to use public networks and stay safe. Why? Because an internet security suite comes with a comprehensive range of cybersecurity tools, anti-virus included.
Most of these tools include features for safer online banking, industry-grade defense against ransomware, web protection, intelligent adaptive protection, dark web monitoring, etc. What’s even better is that you can leave these tools on autopilot, and they will still be able to protect you around the clock.
Use a VPN
A VPN is one of the best solutions for those of you working on public and unsecured networks. It stands for Virtual Private Network. VPN services deliver umbrella-like protection because they act as your bridge to the internet. A VPN encrypts all your web traffic, protecting it from being modified or stolen in transit. Even if someone manages to spy on your connection, the data will be useless to the intrusive party.
VPN also hides your real IP address to allow you to browse the internet anonymously. While thousands of people activate VPNs on their computers, smartphones might be neglected in this area. However, there are many affordable or even free options for making sure that your smartphone is immune to prevalent spying strategies. Even a free VPN on phone can include encapsulation, encryption, access to geo-restricted content, and unlimited bandwidth.
Updates Can Make a Huge Difference
Software applications are not foolproof: they can contain a variety of vulnerabilities. Most of these bugs are benign, but hackers can exploit some of them. Cybercriminals use these backdoors to steal data, install ransomware, or take complete control of your online accounts. Software companies are aware of such threats. So, most of them release updates regularly.
These updates and patches bring new features and improve the old ones. They also fix all the detected bugs that can be used as exploits, which brings us to you and you being on public networks. Make sure that all the devices you use, including your smartphone and tablet, are regularly updated. Most of the new operating systems have an auto-update option: feel free to enable it.You won’t have to worry about manually updating your system and apps.
By following these simple tips, you will be able to take your digital privacy to the next level. Instead of being worried about your security, you will have the privilege of browsing at ease. The more security layers you add to your devices, the better. You will be able to hide your identity online and keep your data and online account credentials safe and sound.
A hotspot — sometimes also called a mobile hotspot, public hotspot, or Wi-Fi hotspot — is a location with a Wi-Fi network, outside of your home or office, where you can connect to the internet.
They’re typically offered by businesses like restaurants, hotels, airports, and malls, though you can also find hotspots in places like libraries and government buildings. While many hotspots are free, some might charge a fee to access them. Restaurants often reserve them for paying customers.
Depending on your cellular plan, you may also be able to turn your phone into a portable hotspot to connect other devices — like tablets and laptops — to the internet using your cellular data.
How to connect to a public hotspot
You connect to a hotspot in the same way you’d connect to any Wi-Fi network.
Many public hotspots are password-protected, so make sure you know both the name of the network and the password, which you can generally find posted somewhere at the hotspot location. You might also need to ask someone, like an employee or attendant, for the password.
1. If you’re using an iPhone, open the Settings app and then tap “Wi-Fi.” If you have an Android phone, open Settings, then tap “Connections” followed by “Wi-Fi.”
2. In the list of Wi-Fi networks, tap the hotspot you’re trying to connect to and then enter the password. In some cases, the hotspot might open a web page with terms of service you’ll need to agree to, or a field to enter the password.
That’s it – you’re now connected. If this hotspot requires a subscription, you might also need to enter payment information, but paid hotspots have become pretty rare.
How to set up a personal hotspot on your iPhone
If you don’t have access to Wi-Fi but need to connect a device like a tablet or laptop, you can use your iPhone as a hotspot. Just note that you’ll need to have a strong cell signal, and your cell carrier needs to support hotspot use. If you don’t know whether your carrier supports it, contact them to ask.
1. Open the Settings app and then tap “Cellular.” Depending on your version of iOS, “Personal Hotspot” may be listed on the main Settings page, not within the Cellular page — if so, tap “Personal Hotspot.”
2. On the Cellular page, tap “Personal Hotspot.” If your current cellular plan doesn’t allow hotspots, there may be an option to “Set Up Personal Hotspot” which will give you a phone number to call or website to visit to upgrade your cell plan.
3. Turn on the hotspot by swiping the button beside “Allow Others to Join” to the right.
4. If you want to customize the password for your hotspot, tap “Wi-Fi Password” and enter a password that you’ll need to use on other devices.
5. Stay on this page – don’t switch to another app or turn the iPhone’s screen off.
6. On the other device, open the Wi-Fi settings and choose the hotspot for your iPhone. Enter the password and you should connect normally. Now you can close the Settings page on your iPhone and use the phone any way you like. As long as you stay in range of the other device, it’ll function as a hotspot.
7. To stop using your iPhone as a hotspot, disconnect from the phone’s Wi-Fi network on the connected device or go back to the Personal Hotspot settings on your phone and turn off “Allow Others to Join.”
How to set up a personal hotspot on your Android
You can share internet access to other devices using your Android phone’s hotspot settings. Again, not all cell carriers support this, so contact your carrier to check their policies.
1. Open the Settings app and then tap “Connections.”
2. Tap “Mobile Hotspots and Tethering.”
3. Tap “Mobile Hotspot.”
4. On the Mobile Hotspot details page, you can set the network’s name and password, then turn it on by swiping the button to the right.
5. Without leaving this page, join the Wi-Fi network on your other device.
6. To stop this hotspot, disconnect from the phone’s Wi-Fi network on the connected device or go back to the Mobile Hotspot settings on your phone and turn the hotspot off.
In a recent survey, 70% of tablet owners and 53% of smartphone / mobile phone owners stated that they use public Wi-Fi hotspots. However, because data sent through public Wi-Fi can easily be intercepted, many mobile device and laptop users are risking the security of their personal information, digital identity and money. Furthermore, if their device or computer is not protected by an effective security and anti-malware product. the risks are even greater.
Wireless Security tips — to help keep you safe on public Wi-Fi
With coffee shops, hotels, shopping malls, airports and many other locations offering their customers free access to public Wi-Fi, it’s a convenient way to check your emails, catch up on social networking or surf the web when you’re out and about. However, cybercriminals will often spy on public Wi-Fi networks and intercept data that is transferred across the link. In this way, the criminal can access users’ banking credentials, account passwords and other valuable information.
Here are some useful tips from Kaspersky Lab’s team of Internet security experts:
- Be aware
Public Wi-Fi is inherently insecure — so be cautious.
Remember — any device could be at risk
Laptops, smartphones and tablets are all susceptible to the wireless security risks.
Treat all Wi-Fi links with suspicion
Don’t just assume that the Wi-Fi link is legitimate. It could be a bogus link that has been set up by a cybercriminal that’s trying to capture valuable, personal information from unsuspecting users. Question everything — and don’t connect to an unknown or unrecognised wireless access point.
Try to verify it’s a legitimate wireless connection
Some bogus links — that have been set up by malicious users — will have a connection name that’s deliberately similar to the coffee shop, hotel or venue that’s offering free Wi-Fi. If you can speak with an employee at the location that’s providing the public Wi-Fi connection, ask for information about their legitimate Wi-Fi access point — such as the connection’s name and IP address.
Use a VPN (virtual private network)
By using a VPN when you connect to a public Wi-Fi network, you’ll effectively be using a ‘private tunnel’ that encrypts all of your data that passes through the network. This can help to prevent cybercriminals — that are lurking on the network — from intercepting your data.
Avoid using specific types of website
It’s a good idea to avoid logging into websites where there’s a chance that cybercriminals could capture your identity, passwords or personal information — such as social networking sites, online banking services or any websites that store your credit card information.
Consider using your mobile phone
If you need to access any websites that store or require the input of any sensitive information — including social networking, online shopping and online banking sites — it may be worthwhile accessing them via your mobile phone network, instead of the public Wi-Fi connection.
Protect your device against cyberattacks
Make sure all of your devices are protected by a rigorous anti-malware and security solution — and ensure that it’s updated as regularly as possible.
Other articles and links related to computer and device security
Use your cell phone to set up a hotspot for easy Wi-Fi access.
Jun 30, 2021 | Share
Brand Guides
Your phone’s Wi-Fi hotspot essentially works like a portable modem and router, giving you internet access while you’re on the go.
Also known as tethering, a phone’s Wi-Fi hotspot uses wireless data to provide a connection for laptops, tablets, and other devices. It’s easy to set up and requires only a hotspot data plan for it to work.
A phone hotspot isn’t as powerful as a standalone hotspot, nor as affordable as a home internet plan. But it comes in handy for short trips and quick fixes—able to connect up 10 to 15 devices at a time while usually hitting speeds in the range of 15 Mbps to 1,000 Mbps (the latter only if you have a 5G phone).
Read on to learn how to make your phone a Wi-Fi hotspot.
Pro tip:
Instead of relying on a hotspot, you can also check to see if you can get a better, cheaper, or faster home internet connection. Use our zip code tool to find out what’s available in your area.
How to turn on a phone hotspot on an iPhone or iPad
Switching on your phone’s hotspot is quick and easy with an Apple iOS device.
Note: If you don’t already have a cellular plan that allows for hotspots, you’ll need to contact your provider to set it up.
Step 1: Go to Settings > Personal Hotspot. Or (depending on the type of iPhone you have) go to Settings > Cellular > Personal Hotspot.
Step 2: Hit the toggle button to turn on the Personal Hotspot. If you don’t have a cellular plan with hotspot data, you may have to tap a button that says Set Up Personal Hotspot, which will prompt you to call your provider.
Step 3: Toggle on the function that says Allow Others to Join.
Step 4: Write down the password. You can change the password by tapping on the text, tapping X to erase it, and typing in a new password of your choice.
Once you’ve turned on your iPhone’s hotspot, you can connect another Wi-Fi enabled device to it by looking up the name of your hotspot on your device’s Wi-Fi menu and typing in the password.
Pro tip:
Hotspot internet speeds can vary depending on the cell service available in your area. Take a speed test to figure out how fast your connection is.
I travel a lot and wanted to know if I could bring my Echo with me and connect it to public Wi-Fi networks to use in hotel rooms. People may also want to use an Echo with a public Wi-Fi network if they live in a dorm or an apartment with free Wi-Fi, so I have shared the information I learned to assist other people who want to connect their Echo devices to public Wi-Fi.
How do I connect my Echo to public Wi-Fi? Some public Wi-Fi networks are able to connect to an Amazon Echo device. A password and/or acceptance of the network’s terms and conditions may be required to connect. Echo devices cannot connect to WPA2-Enterprise Wi-Fi networks.
Many users have reported difficulty connecting their Echo device to a public Wi-Fi network, so in addition to instructions on how to connect your Echo, I have shared some troubleshooting tips.
Connecting an Echo to Public Wi-Fi
Most public Wi-Fi networks still have passwords, so if you are provided a password, you can connect to the Wi-Fi network in the Alexa app normally. However, many Wi-Fi networks use a captive portal rather than a regular Wi-Fi password.
A captive portal is a web browser that will automatically open on your phone, tablet, or computer the first time you use the public network. You have probably seen a captive portal when using the Wi-Fi at a coffee shop, hotel, or other public place. It often requires a password, room number and/or acceptance of terms and conditions.
Connecting Your Echo Device
If you have an Echo that you have previously set up on a different Wi-Fi network, it’s easy to connect it to another network without going through the set-up process again.
- Plug in the Echo.
- In the Alexa app, tap Devices.
- Select the Echo device you want to connect.
- Under Wireless, select Change.
- Select Continue.
- Confirm that you see the orange ring light. If you don’t, press and hold the Action button on the Echo until the light turns orange.
- When you see the orange light, tap Continue.
- Select the Wi-Fi network you want to connect to. If the Wi-Fi network does not have a captive portal, enter the password you were provided.
- If the network has a captive portal, a separate web browser should open automatically. You will need to enter the password or other log-in credentials required by the Wi-Fi network such as a hotel room number. You will most likely have to accept terms and conditions to connect.
- Close the window, and the Alexa app should connect your Echo to the network.
Troubleshooting a Public Wi-Fi Connection
Many users have reported that when they click on the public Wi-Fi network in the Alexa app, the captive portal page does not load or there is an error message. If you are unable to clear the captive portal, the Echo will not connect to the network.
Here are some tips if you are having trouble connecting your Echo to a public Wi-Fi network:
- If you are staying at a hotel, call the front desk. They may be able to authorize your Echo’s MAC address which will bypass the captive portal.
- Keep in mind that some hotels have a limit on how many devices can be connected in a specific hotel room. Check with the front desk to see if there is a limit in your room. You may also be able to purchase Wi-Fi for additional devices.
- If you travel often, I highly recommend purchasing a travel router. It functions just like your home’s Wi-Fi router, but it is smaller for easy portability. With a travel router, you can access the public Wi-Fi network’s captive portal on your phone or laptop and connect your Echo device to the travel router through your other device.
Click here to shop for travel routers on Amazon. If you don’t know much about travel routers, this list of eight of the best travel routers on the market is a good place to start.
Alternative Ways to Connect Your Echo
If you do not want to use a travel router or you do not have access to a Wi-Fi network at all, you can connect your Echo to a mobile hotspot. Mobile hotspots allow you to connect devices to the Internet anywhere there is cell service.
Most phones can function as hotspots, but they will use your phone’s data. Check your phone plan to see if your phone can be used as a hotspot and how much data you have to spare.
How strong and stable your phone’s hotspot is depends on your phone’s signal and battery life. I have found that keeping your phone plugged in at 100% charge while using the hotspot maximizes the strength of your Wi-Fi connection.
If you don’t want to rely on your phone’s hotspot, you can also purchase a seperate one.
This guide reviews six popular hotspots to help you determine which is best for your mobile Wi-Fi needs.